Category: Cyber Security
Find the best cybersecurity tips and tricks to protect your device from cyber threats. These security tips are for both beginners and advanced users.
Guide on Internet Security: How To Protect Yourself Online
What is internet security? Internet security and network security refer to the same thing. However, internet security is slightly different from cybersecurity. In truth, it won’t be wrong to say that internet security is just but a segment of cybersecurity. It is prudent that you clearly understand the distinction between the two. By definition, […]
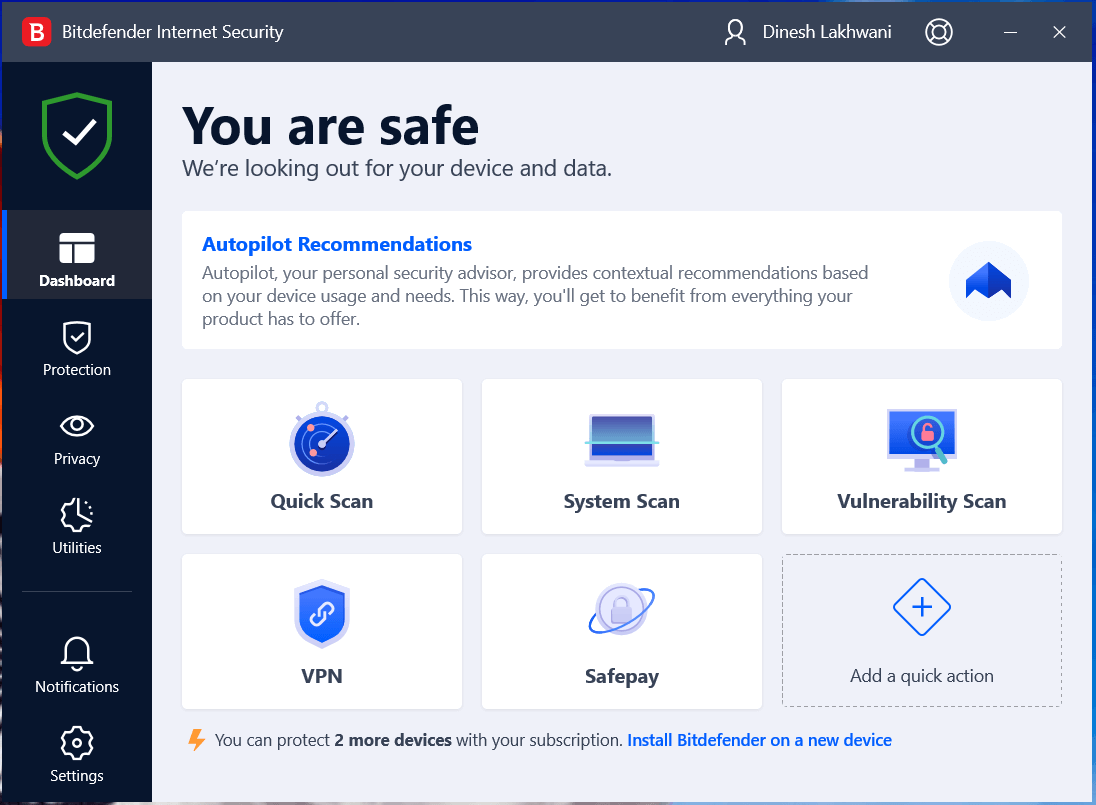
Bitdefender Internet Security Review
As the cybersecurity needs of users are growing, Bitdefender has come up with comprehensive Internet security software that is designed to keep you safe 24/7. Bitdefender Internet Security is a one-stop solution for all your security needs. We’ve got a chance to test this powerful tool and to check its compatibility with other security solutions […]
Top 8 Identity Theft Protection Software in 2026
Internet is the most vulnerable source of identity theft. You never know when your identity is compromised and when you become a victim of ransomware. This article has been designed to introduce best identity theft protection software to protect yourself against ID fraud and stay safe across all areas of your digital life. These best […]
Top 10 Antimalware For Mac in 2026 (Free & Paid)
According to numerous reports, a significant growth in Mac virus attacks has been recorded in the past few years. Cybersecurity is a big issue in front of the world today; it has become very hard day by day to control the malware attacks on Operating Systems. This is the biggest reason that every leading OS […]
What is Email Spoofing and How to Stop It?
As we live in the age of information, it’s safe to say that our lives have become a lot easier with the introduction of internet. Well, you can’t complain when you’re able to pay most of your bills right from your smartphone. But, there’s also another side of the coin here, which is cyber crime. […]
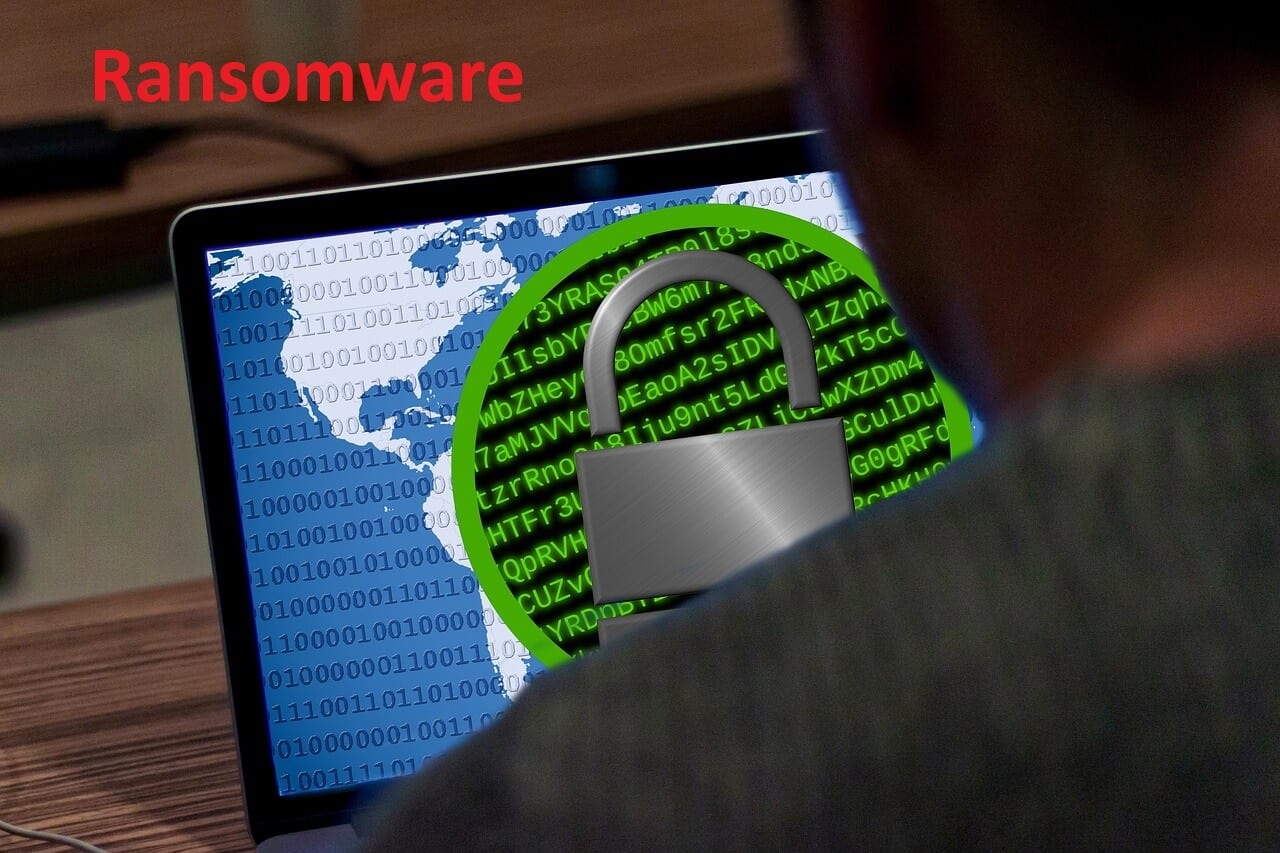
What is Ransomware? How It Works and How to Remove It?
Ever since the computer is introduced to us, the way everything around us operates has been completely changed. For most of the part, it has been extremely good, but it also has brought some unwanted and unpleasant scenarios as well. While computers are being used for pretty much every purpose, we now have millions of […]
10 Best Tips to Improve Online Privacy & Security
Ever since we’ve been introduced to computers, our lives have been completely changed, mostly for good. Today, we operate electronic devices such as computers and smartphones for numerous purposes. Many of us use these devices for work, studies, entertainment, and many more activities. In addition to that, we’re blessed with the internet, through which we […]
Bitdefender Security Tools: Top Internet Security Software
Internet Security is a prominent concerning issue for many people, especially for the business owners. Almost every one of us makes use of internet nowadays for many things. But, the internet can be really dangerous if you don’t follow proper security measures. The last couple of years have seen many disastrous cyber attacks both on […]
9 Best Methods to Keep Your Twitter Account Secure
In addition to the bank account and online shopping portals, it is equally essential to ensure complete security of your Social accounts from harmful malware and adware infections. Just like Facebook, Twitter also provides a ready platform to cybercriminal and the damages it can cause to your personal and professional life can be profoundly disturbing. […]
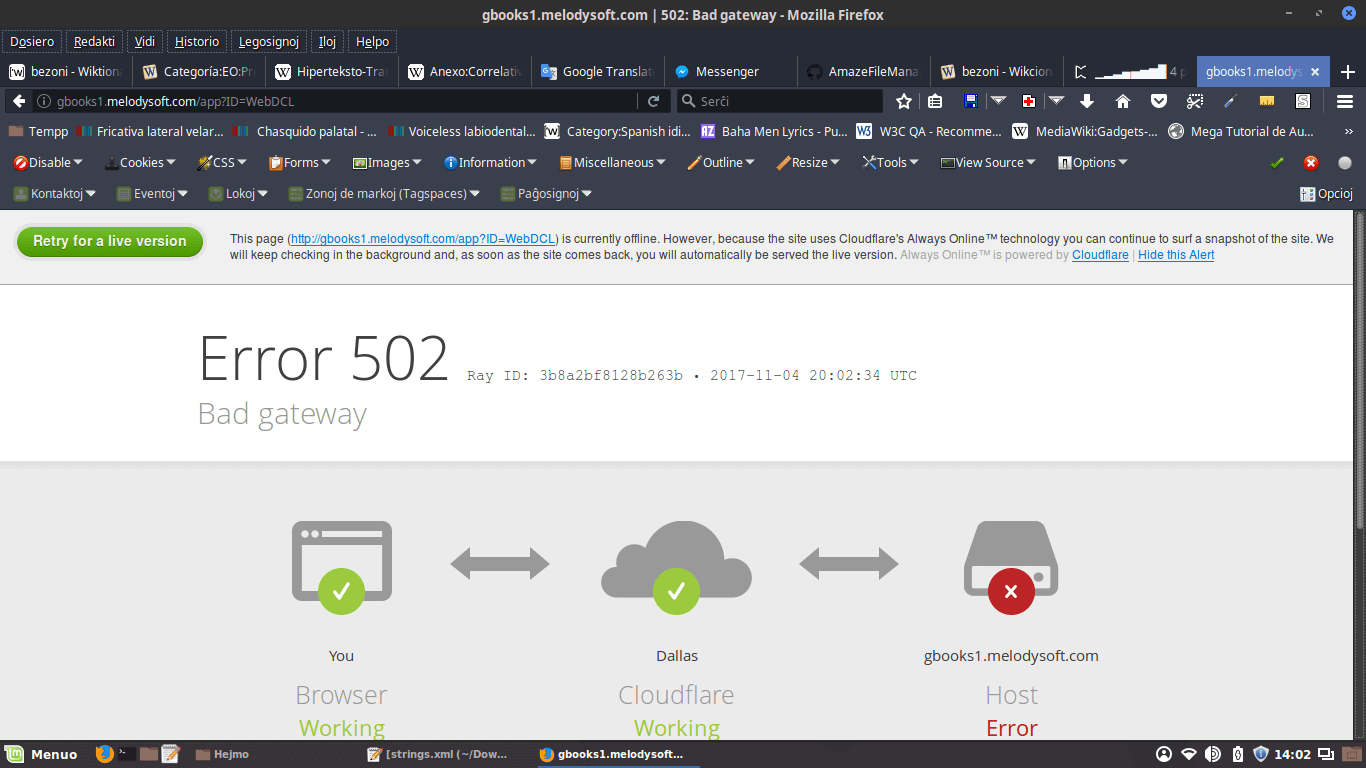
What is 502 Bad Gateway Error and How to Fix It
The inception of internet has made our lives very comfortable, as now we can operate so many things at the comfort of our electronic devices. Almost every person uses internet for appropriate purposes, which makes it a very important part of our daily lives. While browsing internet through several web pages, it’s quite common to […]