Guide on Internet Security: How To Protect Yourself Online
What is internet security?
Internet security and network security refer to the same thing. However, internet security is slightly different from cybersecurity. In truth, it won’t be wrong to say that internet security is just but a segment of cybersecurity. It is prudent that you clearly understand the distinction between the two.
By definition, internet security refers to all the measures, strategies, tools taken by an individual, enterprise, or government to secure the confidentiality and integrity of data and networks.
On the other hand, cybersecurity is more concerned with the general security of a system, websites, servers, computers, and everything in cyberspace.
Is Internet Security Necessary?
What is the essence of internet security to an individual or organization? Isn’t the cost of setting up internet security extremely high for me? These are questions most people ask me whenever I mention to them anything to do with internet security.
I often respond to them with one statement: “investing in internet security is a must-do. However, if you think it will be too costly to invest in internet security, perhaps it would help if you checked out how costly a cyber breach could be.”
RiskIQ estimates that cyber breaches cost businesses $2.9 million every minute, on average. The same report further reveals that enterprises lose $25 every minute to cybercriminals.
One reason to get internet security strategy is to protect yourself from such costs. Internet security is also vital in protecting your sensitive data and users’ data against cybersecurity vulnerabilities.
To stay safe on the internet, you first need to be aware of some of your susceptible threats. Below, I have briefly explained some of the most prevalent cybersecurity threats you should be mindful of.
Internet Security Threats: What the Latest Numbers Say?
Staying safe online is more important than ever. Here are some recent facts that show how big the problem is:
- Cyberattacks happen all the time — more than 2,000 times a day, which means one attack every 39 seconds.
- Ransomware is a big threat — it locks your files and asks for money. There were over 236 million cases last year.
- Phishing emails are everywhere — about 3.4 billion fake emails are sent every day to trick people.
- Schools are top targets — they get attacked more than 3,000 times a week.
- Cybercrime costs are huge — it caused over $10 trillion in damage last year and could reach $23 trillion by 2027.
- AI is helping both sides — while it helps protect people, it also helps hackers make smarter attacks.
- Not enough experts — there’s a shortage of 4 million cybersecurity workers, and it could grow to 85 million by 2030.
- Insurance is getting expensive — prices for cyber insurance went up by 28%.
These numbers show that online threats are growing fast. That’s why it’s so important to use strong passwords, be careful with emails, and keep your software updated.
Common internet security threats Nowadays.
1. Phishing
Phishing is one of the social engineering attacks that hackers use to target their victims. A cyber attacker will masquerade as a genuine entity to dupe a target to open an email attachment or click on a malicious link. Upon clicking the attachment or opening the link, the victim might unknowingly download malware, reveal sensitive data, or freeze their network.
Attackers can also use phishing attacks to gain a position in corporate systems as part of a more significant cyber breach like the advanced persistent threat.
Phishing attacks have become so prevalent in recent times. According to a 2021 ProofPoint State of the Phish Report, 76% of businesses were victims of one or more phishing attacks in 2020. Without a doubt, phishing attacks are the most prevalent social-engineering attacks that you should protect yourself from.
2. Hacking and remote access
Remote working has been gaining momentum recently. Most companies are now opting to have their staff work from home. However, although this might be convenient to organizations, it might also expose your business to several internet security threats.
Remote working typically relies on the internet to exchange data outside the corporate infrastructure. For a seamless exchange of such data, one will require tools and devices, including those outside the control of an organization. As such, remote working is vulnerable to eavesdropping, data manipulation, BYOD threats, and Man-in-The-Middle attacks.
3. Malware
The word malware is a combination of malicious and software, which make up the definition of malware as malicious software. A malware attack is a type of cyber-attack that occurs when attackers craft malicious software and install it on a victim’s computer without the victim’s consent.
Malware attacks have been getting more sophisticated each year. It is one of the primary internet threats that could leave your system in shambles.
4. Ransomware
Ransomware is the most widespread malware attack that poses a significant risk to your entire system. It is sometimes called extortion software because it freezes up your entire system, denying you access to the system until you pay a ransom fee.
Mainly, hackers will demand that you pay the ransom fee in the form of Bitcoin to maintain their anonymity.
According to the FBI, there are over 4000 ransomware attacks each day. If you are keen on the cybersecurity news, you might have heard of the havoc the REvil hacking group has caused recently.
5. Denial of Service
Denial of Service attack is yet another common internet vulnerability. It occurs when legitimate users cannot access a system, device, data, or other network resource because of the actions of malicious cyber attackers. Vulnerable services to denial-of-service attacks include websites, emails, online accounts and all services that require the internet.
The five threats explained above can leave your entire system in devastation. To avoid the heavy repercussions of such attacks, it is wise that you have proper security measures to protect yourself from such threats. In the next section, we will learn about the basic security practices that will protect you from internet threats.
Internet Data Security Tips
● Use SSL Protocol
Installing an SSL certificate is one of the best security measures for staying protected on the internet. The SSL certificate is a digital certificate that combines with the HTTP protocol to form the HTTPS protocol that enables the safe transfer of data and information between two internet points such as website servers and website browsers.
If you have a website, you must ensure that you buy an SSL certificate to safeguard all sensitive data from data interceptions. Most websites, especially startups and small business owners, fear purchasing an SSL certificate because they think they are way too expensive.
However, that is usually not the case. There is no harm when you buy the cheapest SSL certificate. All SSL certificates, whether free or the most expensive ones, give the same encryption strength.
One of the critical things you have to check when buying an SSL certificate is the SSL provider. Some of the best SSL certificates you can go for include Rapid SSL certificate, Comodo SSL certificate and GeoTrust SSL certificates.
● Install an Antimalware and Keep It Updated
It would be best if you had antivirus software to safeguard yourself against internet-related malware attacks and viruses. Remember, we mentioned malware as one of the internet securities threats you are likely to encounter. To protect yourself against such threats, it will be wise to get antimalware software.
You must also remember that new malware and new threats are coming up daily, and this is why you must continually update your antimalware software to keep it well-equipped and, in a position, to fight new and emerging threats.
● Explore the Security Tools You Install
Internet security tools are a must-have. They uphold an internet user’s privacy and help safeguard your system against old and novel cyber vulnerabilities. The tools can help you conduct privacy audits and threat scans to find and remove security threats that might exist in your system. Some of the best security tools that you can consider purchasing include.
- TotalAV
- SolarWinds Security Event Manager
- LifeLock
- Acunetix
● Adhere to Best Password Practices
With internet security, having a strong password should never be an option but mandatory. Passwords protect your entire system against unauthorized entries. However, hackers have been known to break through weak passwords by employing dictionary attacks and brute force attacks.
If you are using a weak password, then your entire system is susceptible to data breaches. You can check out this page for some of the best password practices you must adhere to.
● Use Two-Factor Authentication
Passwords have proved to fail in keeping your system safe from cyber vulnerabilities. Therefore, it would be best if you had two-factor authentication to supplement your passwords. In two-factor authentication, apart from using passwords to authorize entry into your online accounts, you will also use extra authentication factors such as security codes, biometric factors and one-time passwords.
● Use up-to-date software and Operating systems.
Hackers usually figure out new hacking techniques. Old software and operating systems might be ill-equipped to protect your network from security threats. As a security measure, you must always ensure that you update your software to prevent any threats due to loopholes existing in old software versions.
To Wrap Up
Internet security threats can take you out of business. You must ensure that you know some of the threats you are vulnerable to and some of the actionable steps to prevent those threats. This article has tackled the meaning of internet security, cybersecurity threats, and solutions to those threats.
As a best practice, always ensure that you use multiple security solutions to strengthen your security walls. Lastly, do not forget to backup, just in case things go south.
Popular Post
Recent Post
New Features Coming in Windows 11 This Year [2026]
Microsoft is always working to make Windows better. This year is no exception. The company has announced and rolled out several exciting updates for its users. These updates touch almost every part of the operating system. From the Start menu to system settings, changes are arriving fast. If you use Windows daily, you will want […]
Top 14 Duplicate Photo Finder and Remover For Windows [2026]
Introduction: Photos pile up fast. Well, yes! You take ten shots of the same moment. You download the same image twice. You back up your folder and forget you already did it. Before you know it, your storage is packed with copies. A good duplicate photo finder helps you take back that space without losing […]
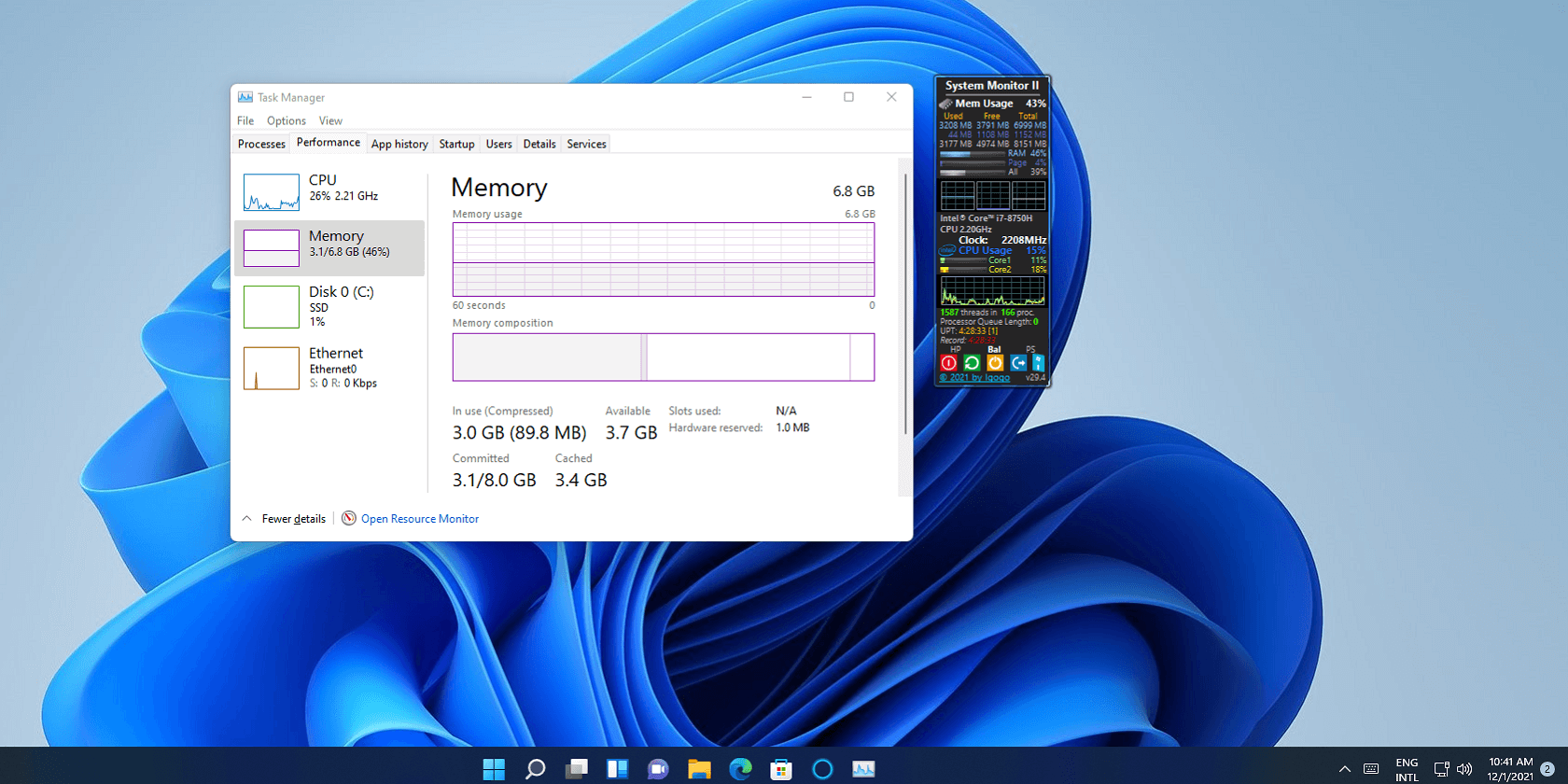
Advanced System Settings on Windows 11: Complete Guide
Windows 11 is a powerful operating system. It comes with many features that most users never explore. One of the most useful areas is the System Properties panel. This is where you can control how your computer performs, starts up, and handles memory. Many users only change basic settings like wallpaper or display options. But […]
21 Advanced Windows Security Settings: Latest Updates
Introduction: Your computer holds a lot of important data. From personal photos to work files, everything sits on your Windows system. That is why protecting it properly matters more than ever. Windows security settings have come a long way. Microsoft keeps adding stronger layers of protection with every update. Most users never go beyond the […]
Security Upgrades of Microsoft Windows in This Decade [Complete Guide]
Introduction Microsoft has been working hard to make Windows safer every year. Cyberattacks are growing fast. Hackers are smarter now. They target millions of Windows users every single day. That is why Microsoft has added many powerful new security upgrades of Microsoft Windows since 2020. These upgrades protect your data, your identity, and your device […]
How To Link a Microsoft Account to a Digital License on Windows [2026]
Most people never think about Windows activation until it suddenly stops working. Something as simple as replacing hardware or reinstalling Windows can cause the system to lose its activated status. Linking your Microsoft account to your digital license beforehand helps prevent unnecessary trouble and makes activation recovery much easier later on. Many people using Windows […]
Monthly Round Up: All Big Incidents Happened for Windows Users in The Month of April 2026
Windows users had a turbulent April 2026. On April 14, Microsoft rolled out its scheduled Patch Tuesday security updates, a routine release meant to close vulnerabilities and resolve known issues. What followed was anything but routine. Rather than strengthening systems, the updates triggered a cascade of fresh problems across Windows 10, Windows 11, and Windows […]
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]