What is Ransomware? How It Works and How to Remove It?
Ever since the computer is introduced to us, the way everything around us operates has been completely changed. For most of the part, it has been extremely good, but it also has brought some unwanted and unpleasant scenarios as well. While computers are being used for pretty much every purpose, we now have millions of computers all around the world.
Well, there’s a darker side to this phenomenon, which is the aspect of cyber attacks. Even though digital threats are nothing new to us, but recently they’ve been growing stronger with exponential pace.
The latest threat that shook the digital world is ransomware, especially popularized by the ‘wannacry’ attack. Thousands of people have become victim to this ransomware attack. To know what is ransomware and other related information, keep on reading.
What is Ransomware?
Ransomware is a type of malicious software, which is also shortly known as malware. It attacks vulnerable computers and gets access to all the files in the devices. After achieving access, it then encrypts those files and demands money as ransom from the device owner.
Unless the person pays the ransom amount, the computer will stay in locked mode, making it impossible to access your data. Let’s have a look at some of the popular ransomware types:

Image Source: condecdn.net
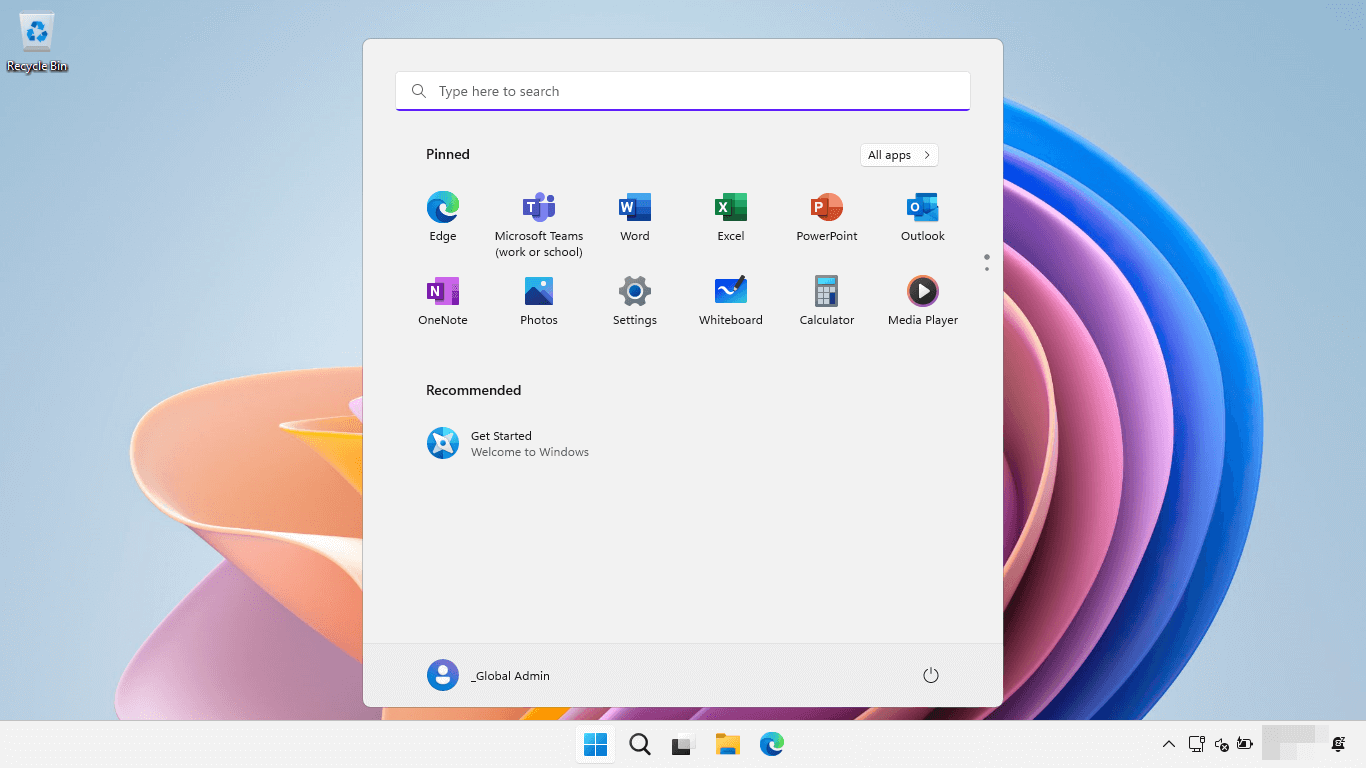
- Scareware: Well, you don’t really have to be scared just because it has the term ‘scare’ in its name. Basically, it’s a fake program that claims itself to be a genuine security program. It then offers you assistance in fixing various types of system issues. If you accept the offer you’ll be asked to pay subscription fee. If you still proceed with that, you will just lose money and nothing gets fixed. To be precise, it’s just a scamming method. This type of ransomware is deployed through pop-up, which if you ignore, you’ll be just fine.
Image Source: fraudwatchinternational.com
- Doxware: Now, we move to the next level of ransomware threats, which is Doxware, alternatively known as leakware. If your device is infected with this type of malicious software, you’re almost doomed. As we all store confidential and personal files on our devices, doxware, after attacking your computer, threatens to leak your information unless you pay ransom money.
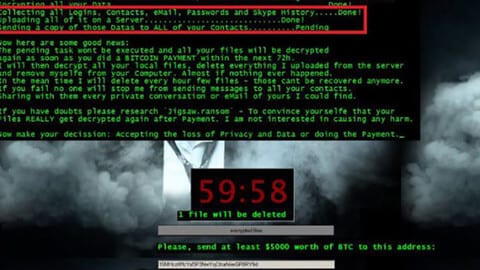
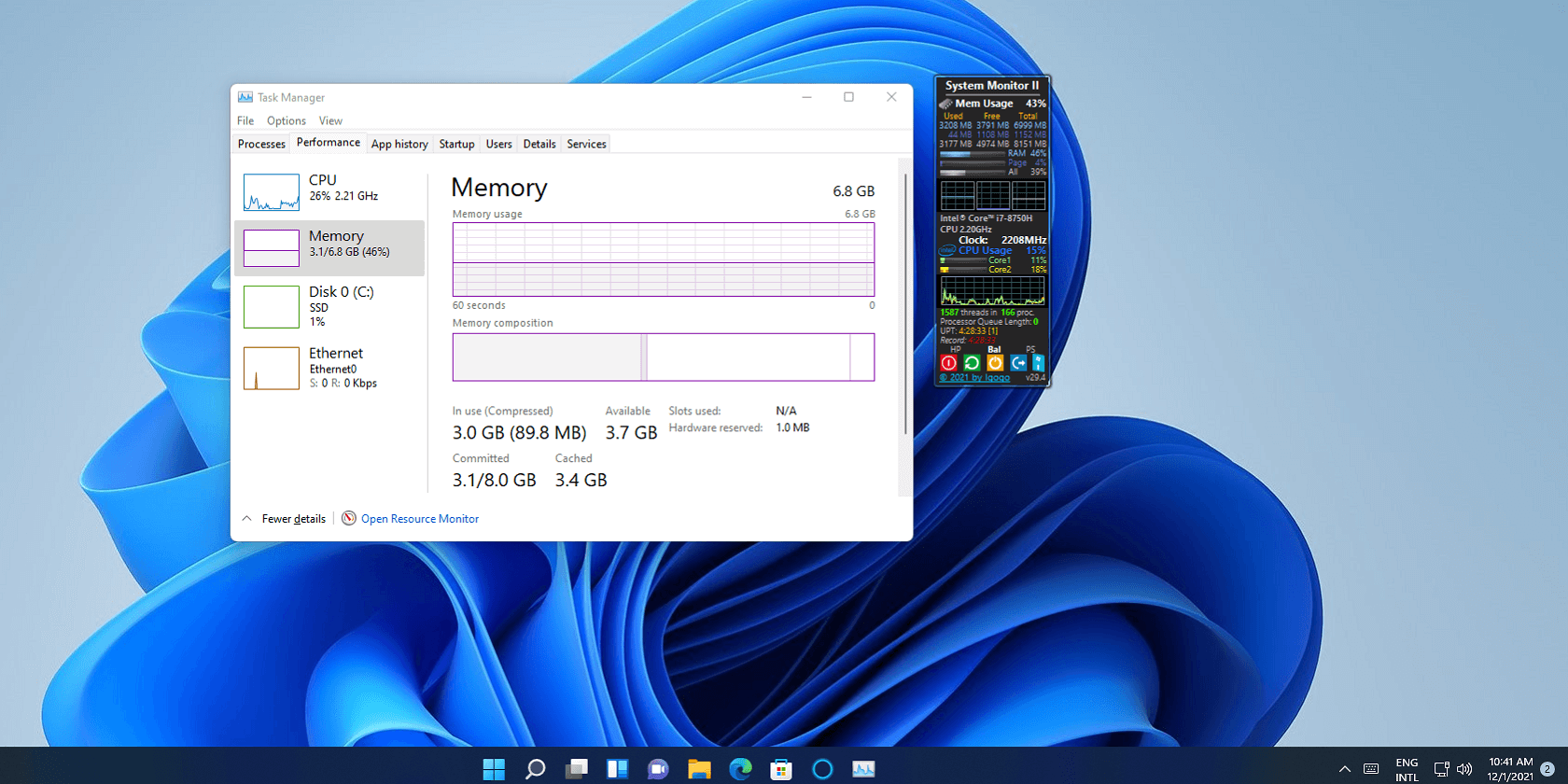
Image Source: thewindowsclubco
- Encrypting Ransomware: This is the most lethal form you can get from ransomware. Many famous cyber attacks come under this category, as they’ve bamboozled a lot of people around the world. Basically, hackers use this attack method to get hold of a device and then to encrypt it completely. Unless you pay the demanded amount of money as ransom, you can’t get access to your device and files in it. It is as dangerous as it gets if you’ve fallen victim to this category.
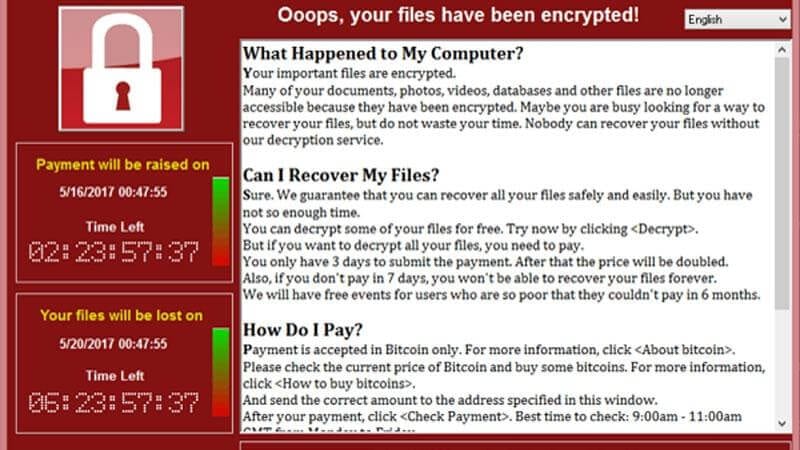
Image Source: computerworlduk.com
How does Ransomware work?
As discussed above, a ransomware program attacks your computer and then encrypts the data in it. You can get access to your files only if you pay the ransom money. So, to understand the process of how it works in a better way, let’s have a look at some of the key steps involved in the attack:
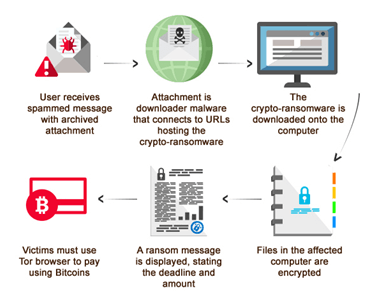
Image Source: trendmicro.com
- Generally, it all starts with the deployment of the malware into your device, either through an e-mail, pop-up, or any other source.
- When the user clicks on the source, which is disguised as an important item, a redirection to a new landing page takes place.
- Once the website redirection happens, the server hosting the ransomware begins communicating with your device.
- As soon as a vulnerability is found in the victims’ computer, the malware file download begins.
- The final step involves the encryption of the victim’s files and information, after which a message appears with payment details.
How to remove Ransomware from your device?
Ransomware not only attacks corporate computers, but also targets commoners like you and me. Once attacked, it’s very difficult to get rid of it. As they say, prevention is better than cure. If you want to be safe and secure, you must follow several precautionary measures. Here are a few things that you should do:
- Never click on random links and suspicious emails.
- Try to download any type of files from only official websites.
- Don’t use pirated websites and services to download files.
If you’ve been attacked by ransomware, you should install anti-ransomware software to get rid of the malicious program. But, there’s no 100% guarantee that a security program will help you in such instances. It’s better to use a security software beforehand, so that it will prevent any type of attacks taking place.
Final Verdict
Now, you must be aware of what is ransomware and how it works. As you’ve also learnt how to prevent and remove it, now it’s time for you to take precautionary measure to stay safe. Download and start using a reputed anti-ransomware software to avoid any type of future attacks.
Popular Post
Recent Post
How To Link a Microsoft Account to a Digital License on Windows [2026]
Most people never think about Windows activation until it suddenly stops working. Something as simple as replacing hardware or reinstalling Windows can cause the system to lose its activated status. Linking your Microsoft account to your digital license beforehand helps prevent unnecessary trouble and makes activation recovery much easier later on. Many people using Windows […]
Monthly Round Up: All Big Incidents Happened for Windows Users in The Month of April 2026
Windows users had a turbulent April 2026. On April 14, Microsoft rolled out its scheduled Patch Tuesday security updates, a routine release meant to close vulnerabilities and resolve known issues. What followed was anything but routine. Rather than strengthening systems, the updates triggered a cascade of fresh problems across Windows 10, Windows 11, and Windows […]
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]
Change Time Format On Windows: Complete Guide
Windows show time in different ways. Some people prefer the 12-hour clock with AM and PM. Others like the 24-hour format, also called military time. Knowing how to change time format on your Windows PC is a simple but useful skill. It helps you stay comfortable with your display and avoid confusion. Many users never […]
How To Get Help With Paint In Windows [2026]
Microsoft Paint has been around for decades. It comes with every version of Windows and is one of the easiest tools to use. But even simple tools can cause trouble. If you have ever felt stuck while drawing or editing an image, you are not alone. Many people look for help with Paint in Windows […]
How To Toggle Bluetooth Settings Easily on Windows [2026]
Bluetooth is a key feature on any Windows computer. It allows you to connect devices like headphones, keyboards, mice, and speakers without using wires. Many users rely on it daily, so it helps to know how to switch Bluetooth on or off quickly whenever needed. Sometimes you just want to turn Bluetooth on or off […]
System Restore: Complete Guide for Windows 11
Introduction: Your Windows 11 PC can run into problems at any time. A bad update, a new app, or a wrong setting can break things fast. When that happens, you need a quick fix. System Restore is one of the best built-in tools Windows offers for these moments. It helps you roll back your PC […]
Setting Up Default Audio Device: Complete Guide [2026]
Introduction: Sound is a big part of how we use computers every day. Whether you are watching a movie, joining a video call, or listening to music, your audio needs to work properly. Setting up default audio device is one of the first things you should do when you connect new speakers, headphones, or a […]