9 Best Methods to Keep Your Twitter Account Secure
In addition to the bank account and online shopping portals, it is equally essential to ensure complete security of your Social accounts from harmful malware and adware infections.
Just like Facebook, Twitter also provides a ready platform to cybercriminal and the damages it can cause to your personal and professional life can be profoundly disturbing.
Recent years have seen a considerable increase in the number of security breaches, the latest victim being Katy Perry.
It is quite impossible for someone to prove that their Twitter account is 100% secure from online dangers.
Nothing is entirely safe in the online world. Below mentioned are 10 best methods which you can follow to increase the security and privacy of your Twitter Account.
1. Choose a strong password
In the light of the ongoing information breaches, following healthy password habits is one of the most fundamental steps towards security. Mentioned here are few of the Do’s and Don’ts users need to follow while setting a password.
Do’s
- The password should have at least 10 characters. Longer the password stronger it is.
- Should be a complex mix of alpha-numeric characters.
- Users should keep different passwords for different sites.
Don’ts
- Passwords should never contain any personally identifiable information like name, Date-of-birth, etc.
- Should not be a combination of keyword sequence like “querty.”
- No two sites should have the same password.
Furthermore, you can add another level of security by opting to “require personal information to reset my password.” This means if you forget your password, you will be prompted to provide your registered email address or mobile number for the confirmation code or OTP to access the reset password link.
2. Use SMS Two-Factor Authentication
The Two-step verification features ads an additional layer of security.
Also knows as the Two-Factor authentication, it implies that anyone who endeavors to log in to their Twitter account would require a security key sent on their registered mobile number.
Users having access to both login password and one-time code can successfully login to their accounts.
You may follow the below procedure to set up a login verification.
- Access the Accounts section from Twitter preferences window.
- Choose the “Security” option from the new window and click on the “Set up login verification” tab.
- Specify preferences and requirements and click on the “Start” button.
- Enter your password and then click on the verify button.
- Confirm your registered mobile number and then click on the “Send Code” tab.\
- Input the one-time code to confirm it.
3. Ensure that you are on a correct domain
Phishing sites can often display fake login pages and trick users into disclosing their login details. Users are recommended to check the URL before entering their credentials. A genuine URL should always read as https://twitter.com/ or https://twitter.com or https://twitter.com/login.
4. New Login alerts
Whenever a login happens from a new device, users will receive email notifications. This is an added feature which Twitter uses to confirm who has logged into the account.
For user logging in using the incognito mode, they will receive alerts each time they attempt to access their account.
5. We will never ask you for your password
Another important part is that Twitter never asks for any login details or downloads from non-twitter sites. Never open or access any email which you are doubtful about. If you forget your password, you may consider resetting it with the twitter.com password reset link.
6. Evaluating links of Twitter
Often it is seen that Twitter users post shortened links and URL’S to make thing easy for them. However, at times such shortened links can confuse users and make it difficult for them to tell where the link goes to.
7. Email address update
Evert time users change their registered email id they will receive a notification on the previously registered email id.
8. Keep your system and browser up-to-date
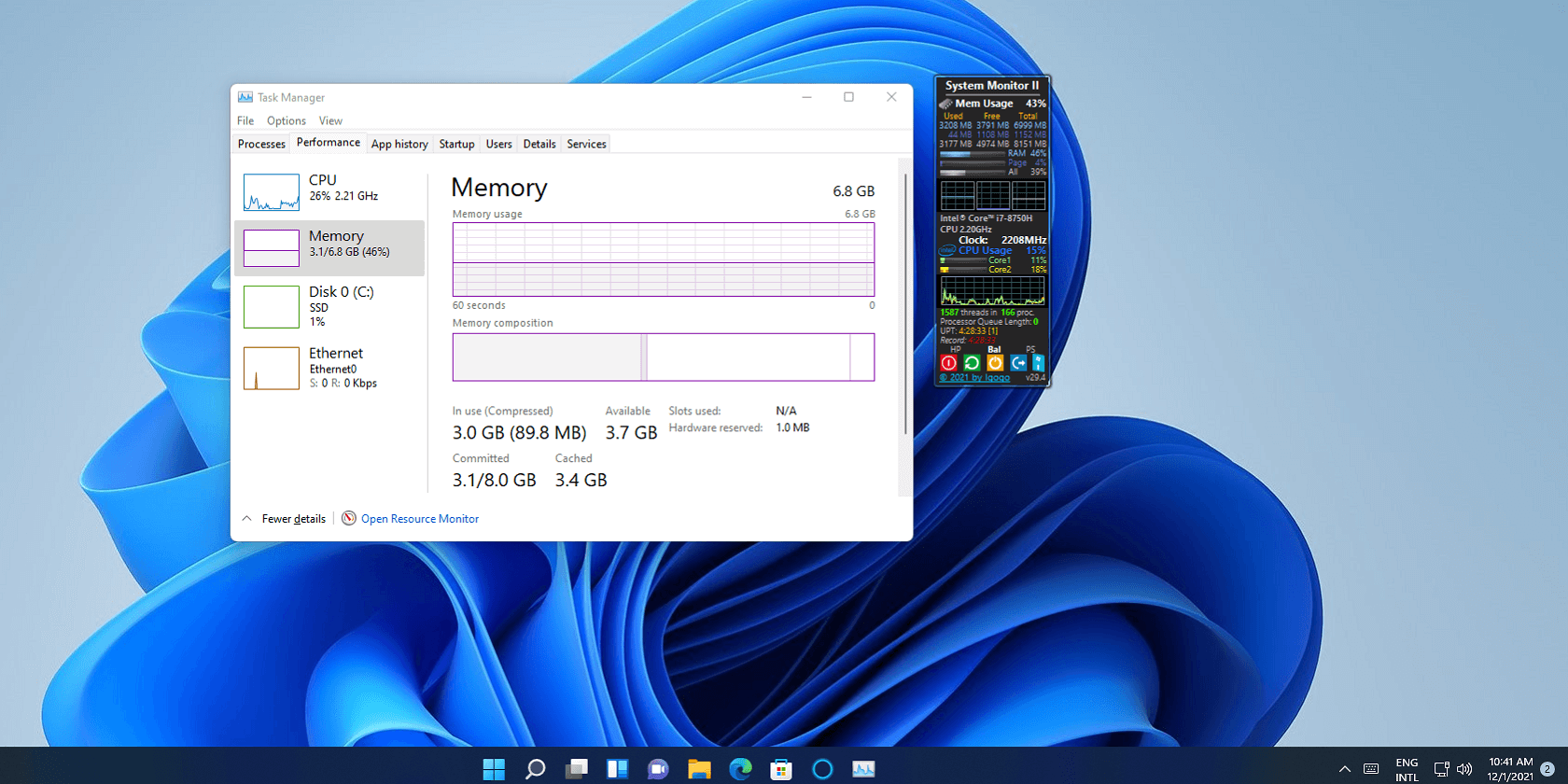
Users are advised to keep their system up-to-date along with the browser. Cybersecurity researchers keep releasing security patches from time to time to ensure complete protection from malware, adware and other PC threats. If you are using a public network make sure that you log-out correctly after every sign-in.
9. Beware of third-party applications
Using your Twitter account to access third-party account may give unwanted access to your account to outsiders. If you experience anything fishy make sure that you remove that app as soon as possible.
Conclusion
At the point when a system turns out to be exceptionally well known, hackers and scammers will be all prepared to exploit any vulnerabilities. They know they have potential new casualties and they won’t miss any chance to assault.
However, if you follow basic online hygiene and set up all the security layers and keep sound propensities, you’ll have the capacity to limit the dangers of a rupture and malware attack.
Popular Post
Recent Post
Resolving Screen Flickering Problems On Windows 11/10: Complete Guide
Introduction Screen flickering is a common issue in both Windows 10 and Windows 11 systems. It may appear as quick flashes, blinking lines, or unstable brightness on the screen. This problem can interrupt your work and make it difficult to focus for long periods. Many users notice this issue after installing updates, changing drivers, or […]
Adjusting Volume Balance Settings On Windows 11: Complete Guide
Introduction: Sound is an important part of using a computer every day. You may watch videos, listen to music, attend online meetings, or play games. In all these tasks, clear and balanced sound makes a big difference. Sometimes, audio may not feel right. One side may sound louder than the other. This can make listening […]
Resetting Audio Settings: How To Reset Sound Settings [2026]
Introduction Sound issues can affect your daily work and entertainment. You may notice that your speakers stop working, or your headphones produce unclear audio. In some cases, the sound may suddenly drop or become uneven. These problems can be frustrating, especially when you do not know the cause. Many users try random fixes, but that […]
How To Troubleshoot Miracast Connection Issues On Windows
Introduction Miracast is a useful feature that allows you to share your screen without using cables. It lets you mirror your Windows device to a TV, monitor, or projector. This feature works through wireless display technology. Many people use it for work meetings, school presentations, and home entertainment. It removes the need for HDMI cables […]
How To Fix Issues Downloading from the Microsoft Store On Windows
Introduction: Downloading apps from the Microsoft Store should be a simple task. You open the Store, search for an app, and click install. In most cases, the process works without any problem. However, there are times when the download does not start. In some cases, it may stay stuck at a certain percentage. You may […]
How To Fix Windows Update Issues Easily On Windows [2026]
Introduction Windows updates play an important role in keeping a computer stable and secure. They bring new features, fix known bugs, and improve overall performance. When updates work as expected, the system runs smoothly. However, when they fail, users often face slow performance, missing features, or security risks. This is why it becomes important to […]
How To Check If Your PC Is Infected? [Complete Guide]
Computers now sit at the center of almost everything we do. Well, yes! From sending emails to watching videos, we depend on them without much thought. Because of this, even a small issue can disrupt daily tasks. One common problem is hidden malware. It does not always show clear signs at first. It can enter […]
Repair Apps And Programs: Repair Apps That Aren’t Working
Computers have become an essential part of everyday life, supporting work, study, communication, and entertainment. Most of these activities rely on apps and programs, so when one stops functioning, even simple tasks can be disrupted. Common problems include error messages, frozen screens, or apps that fail to open. On Windows systems, such issues often arise […]
Troubleshooting Microphone Privacy Settings: Complete Guide
Sound is a basic part of how we use computers today. People attend meetings, record audio, speak to others, and use voice tools almost every day. A working microphone makes all these tasks easy. When the microphone fails, even simple work becomes difficult. Many users first think the device is broken. In reality, the issue […]
Windows Sound Settings – Sound Control Panel: Complete Guide
Sound plays an important role in how we use a computer every day. It supports both work and leisure. You need it for meetings, videos, music, and alerts. When audio fails, even simple tasks become difficult. Many users feel stuck when sound issues appear. This usually happens because they are not familiar with Windows Sound […]