What Is Onion over VPN and How Does It Work?
Security and privacy are the two main challenges of any modern digitized system. While data is vulnerable during the transfer from one system to another, unauthorized access compromises the privacy of the crucial information.
Hence, the IT world is struggling to develop modern tools and technologies that add an extra layer to the existing security features. The leading security services like Norton offer much-needed protection and the ideal combination of Onion over VPN.
Let us go through the concept of this merging of two different security tools in one, its practical work in safeguarding any system followed by some quick questions on the same. However, before jumping to combination, let us understand Onion and VPN independently.
What is Onion?
The data in the onion network are encrypted and then transmitted through network node series like the onion layers. These network nodes are called the onion routers. The message or data arrives at the destination when the final layer is decrypted.
The protection of the identity is at its best as every next layer knows about the preceding layer details only. It is also called the Tor network.
What is VPN?
The Virtual Private Network or VPN creates a simple private network from any public internet connection.
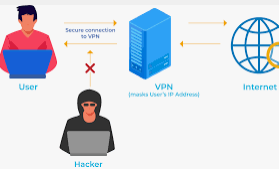
Hence, VPNs mask the IP address of the internet user, and all the actions remain highly untraceable. Therefore, it is perfect for devices at high risk of losing data protection when connected to public internet connections.
What is Onion over VPN?
It is common and quite understandable to desire the double benefits of the onion network and VPN. Hence, the Onion over VPN was created. Also known as Tor over VPN, this setup passes the internet traffic through VPN and then through the Onion network before sending it to the internet servers. In other words, the internet user’s identity remains anonymous, and there is no possible option to trace back the connection.

It simultaneously uses the Tor browser and VPN for any inbound or outbound data traffic. The primary purpose of this setup is multi-layer encryption using the benefits of the onion network and VPN at the same time. As a result, it significantly covers the double VPN benefits and offers easy use and high-end security uses.
How does Onion over VPN work?
It is easy to understand the workflow in the Onion over the VPN network. The primary needs of such a setup are a good internet connection, VPN, and Onion browser. The VPN providers often offer Onion over VPN setup as an in-built feature in their app. Let us understand the inbound and outbound internet data flow separately for the step-by-step working of this effective setup.
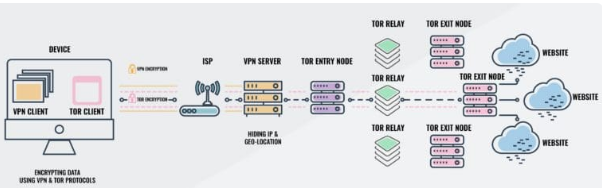
Outbound internet data flow:
- The data from the device is encrypted using the VPN.
- The encrypted data from the VPN is again encrypted for adding a layer of encryption to the data.
- The double-encrypted data is sent to the VPN server.
- Once data is received by VPN, it decrypts the data. The Onion Browser or Tor browser still encrypts the data from the VPN at this stage.
- According to the requirements, this encrypted data is sent through the Tor browser to the dark web or the clear web.
- For the dark web, data is decrypted once it reaches the destination.
- For clear web, data is decrypted at the node of the onion browser and then is sent to the World Wide Web.
Inbound Internet data flow:
- The app, service provider, or website data is sent to the Tor browser.
- The Tor browser receives the data and encrypts it.
- The encrypted data from the Tor network is sent to the VPN server.
- The VPN server adds another layer of encryption to the encrypted data from the Tor network.
- The double-encrypted data is sent to the user’s device.
- The tor browser decrypts the data sent to the device.
- The VPN again solves the data from the Tor browser.
Why is Onion over VPN used?
Security and privacy may seem like the only two main benefits of Onion over VPN, but there is a lot more technical.

The main advantages of this setup include:
- It offers exceptional levels of seamless internet connectivity as the VPN hides the home IP address and prevents it from entering the Onion network. Hence, the system can’t generate the IP address of the user.
- It offers end-to-end data encryption for the user. Even the VPN provider can’t access the data going to the onion network due to the additional encryption layers over the VPN. It is hard to trace back a connection made using this setup. The possibility of an unauthorized node in the Onion network is best handled by the VPN which prevents data access to any outside entity.
- It is an easy-to-use setup. Moreover, multiple VPN service providers offer Onion over VPN setup as a built-in feature. Thus, it eliminates the use of any external browser, and this setup is achieved using a single click only.
- It is possible to access the restricted websites that are not possible using the independent onion network. Hence, many users benefit from accessing dark websites with the combination of Onion over VPN.
FAQ:
- What is the simple flow in Onion over VPN?
The internet details from the device go through the VPN server and then pass through the Onion network in this setup. After going through the Onion network, the details reach the World Wide Web.
- What do I need to use Onion over VPN?
The main requirements of using this setup include high-speed internet access, a VPN, and Onion or Tor browser. Depending on the requirements, the user can go for any other browser than the Tor browser.
- How to use Onion over VPN setup?
It is easy to use this security setup. First, the user can open the VPN app with in-built support to this combination. Then, once a VPN connection is achieved, the Tor or Onion browser can be accessed for quick internet surfing.
- Do VPNs offer in-built Onion over VPN support?
Some VPNs like NordVPN, ProtonVPN, etc. comes with in-built support to the Onion over VPN combination. It allows quick access to any application without configuring it to the independent Onion browser.
- Is Onion over VPN different from VPN over Onion?
Yes, both these security settings are quite different from one another. It isn’t easy to set up a VPN over Onion and has a different set of advantages and purposes than the useful combination of Onion over VPN.
Wrapping Up:
Onion over VPN wins by large numbers when it offers modern security and privacy standards to any device. The protection of browsing history from the independent VPN, hiding real IP addresses, and performing all critical tasks safely is turning many VPN providers to offer in-built support to this combination.
When compared with the VPN over Onion, the Onion over VPN is easy to setup, understand, and comes with a long list of security and privacy benefits for any personal or professional user.
Popular Post
Recent Post
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]
Change Time Format On Windows: Complete Guide
Windows show time in different ways. Some people prefer the 12-hour clock with AM and PM. Others like the 24-hour format, also called military time. Knowing how to change time format on your Windows PC is a simple but useful skill. It helps you stay comfortable with your display and avoid confusion. Many users never […]
How To Get Help With Paint In Windows [2026]
Microsoft Paint has been around for decades. It comes with every version of Windows and is one of the easiest tools to use. But even simple tools can cause trouble. If you have ever felt stuck while drawing or editing an image, you are not alone. Many people look for help with Paint in Windows […]
How To Toggle Bluetooth Settings Easily on Windows [2026]
Bluetooth is a key feature on any Windows computer. It allows you to connect devices like headphones, keyboards, mice, and speakers without using wires. Many users rely on it daily, so it helps to know how to switch Bluetooth on or off quickly whenever needed. Sometimes you just want to turn Bluetooth on or off […]
System Restore: Complete Guide for Windows 11
Introduction: Your Windows 11 PC can run into problems at any time. A bad update, a new app, or a wrong setting can break things fast. When that happens, you need a quick fix. System Restore is one of the best built-in tools Windows offers for these moments. It helps you roll back your PC […]
Setting Up Default Audio Device: Complete Guide [2026]
Introduction: Sound is a big part of how we use computers every day. Whether you are watching a movie, joining a video call, or listening to music, your audio needs to work properly. Setting up default audio device is one of the first things you should do when you connect new speakers, headphones, or a […]
Emptying the Recycle Bin In Windows: Complete Guide
Introduction: When a file is deleted in Windows, it is not erased immediately. It is first sent to the Recycle Bin, where it stays until it is removed permanently. Clearing the Recycle Bin is a quick way to regain storage space. Many users do this often to keep their system clean and working properly. Knowing […]
How To Close Games Assist: Simple Methods to Try
Introduction Do you have a feature on your device that keeps popping up while you play games? Many users want to know how to close Games Assist because it shows up at the wrong time. It can be distracting. It can slow down your game. And sometimes, you just do not need it running in […]
Optimizing Graphics Performance: Complete Guide [2026]
Introduction: If your games stutter or your videos look choppy, your graphics might need some help. Optimizing graphics performance is one of the best things you can do for your PC. It makes everything look better and run faster without buying new hardware. Many people think better visuals require expensive upgrades. But that is not […]