How To Detect And Remove Keylogger From Windows PC?
Introduction
Keyloggers are a famous tool hackers use to obtain passwords and other sensitive data. All they need is access to the device to detect keylogger in Windows PC. Once set up, the keylogger will operate silently in the background and capture the keystrokes you make on a physical or virtual keyboard.
There are various kinds of keyloggers; some must be installed physically, while others are software-based. Keylogger in Windows PC constitutes a significant security hazard to Windows computers. These malicious programs can be used to keep track of keystrokes and gain access to sensitive information, making them a target for surveillance instruments and hackers.
It is crucial to identify these threats before they can cause any damage. Here are certain bets methods to detect Keyloggers in PC and remove them while maintaining the performance of the system.
Primary Reason That Keylogger Is Risky:
A keylogger is a program or device that records the strokes made on a keyboard or device. Hardware keyloggers can be installed by USB or a malicious driver, making them easy to identify and disable. On the other hand, software keyloggers may be hidden and more challenging to detect.
Remote keylogger in Windows PC do not slow down system performance like regular viruses and Trojans, but they can be even more damaging as they can reveal your confidential data to others. It includes commercial data, credit card information, PINs, passwords, and anything you have posted online anonymously.
Keyloggers can be highly sophisticated, using keystroke analysis to outline clients based on the sequence and model of their keystrokes. For a keylogger to be active, it must be appropriately installed on the computer. Different types of keyloggers vary in terms of their level of complexity and the potential threat they pose. Here are some of the categories:
- General Spyware: Traditional keyloggers can be inserted onto a device through malicious means, such as a suspicious email attachment, a social media download, or a torrent website. However, Windows Defender or other anti-malware programs typically block these malicious programs.
- Hypervisor based: Virtualization technology can create a replica of the operating system, which allows sophisticated keylogger in Windows PC to capture all keystrokes. However, these types of cyber threats are uncommon.
- Browser based: Malicious webpages may attempt to gain access to your system through web-form-based keyloggers in PC, CSS scripts, or Man-In-the-Browser attacks. Thus, if your computer runs Windows 11 or 10 with the Windows Security application enabled, these potential threats are thwarted immediately.
- Kernel Level: These are even more dangerous as they can hide beneath the Windows operating system in the rootkit format, making them hard to detect.
The Process To Detect And Remove Keyloggers:
Keyloggers can cause the same type of damage to iPhones, Macs, PCs, and Androids as other forms of malware. If you think keyloggers in Windows PC have infiltrated your Windows system, there are steps you can take for detecting and eliminate them. Here is the straightforward method described:
1. Take The Initial Support Of The Task Manager:
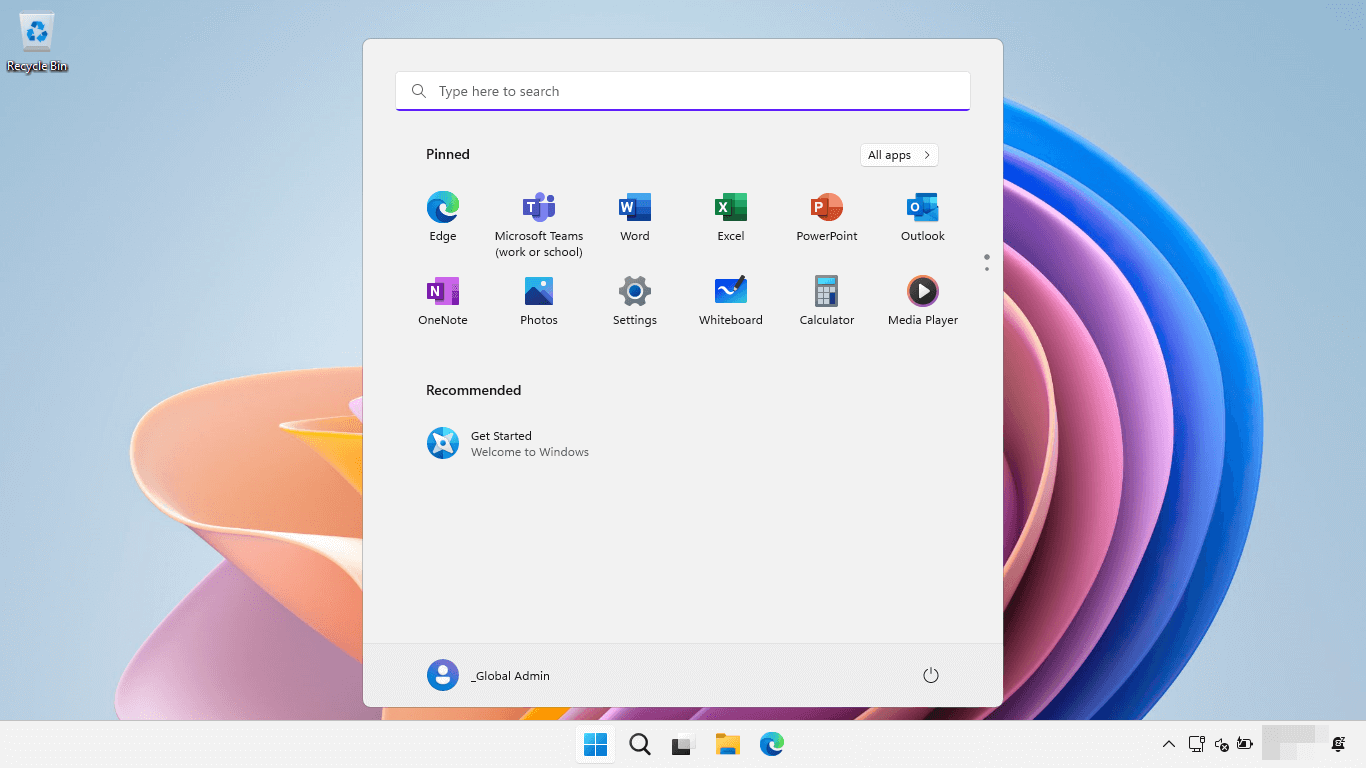
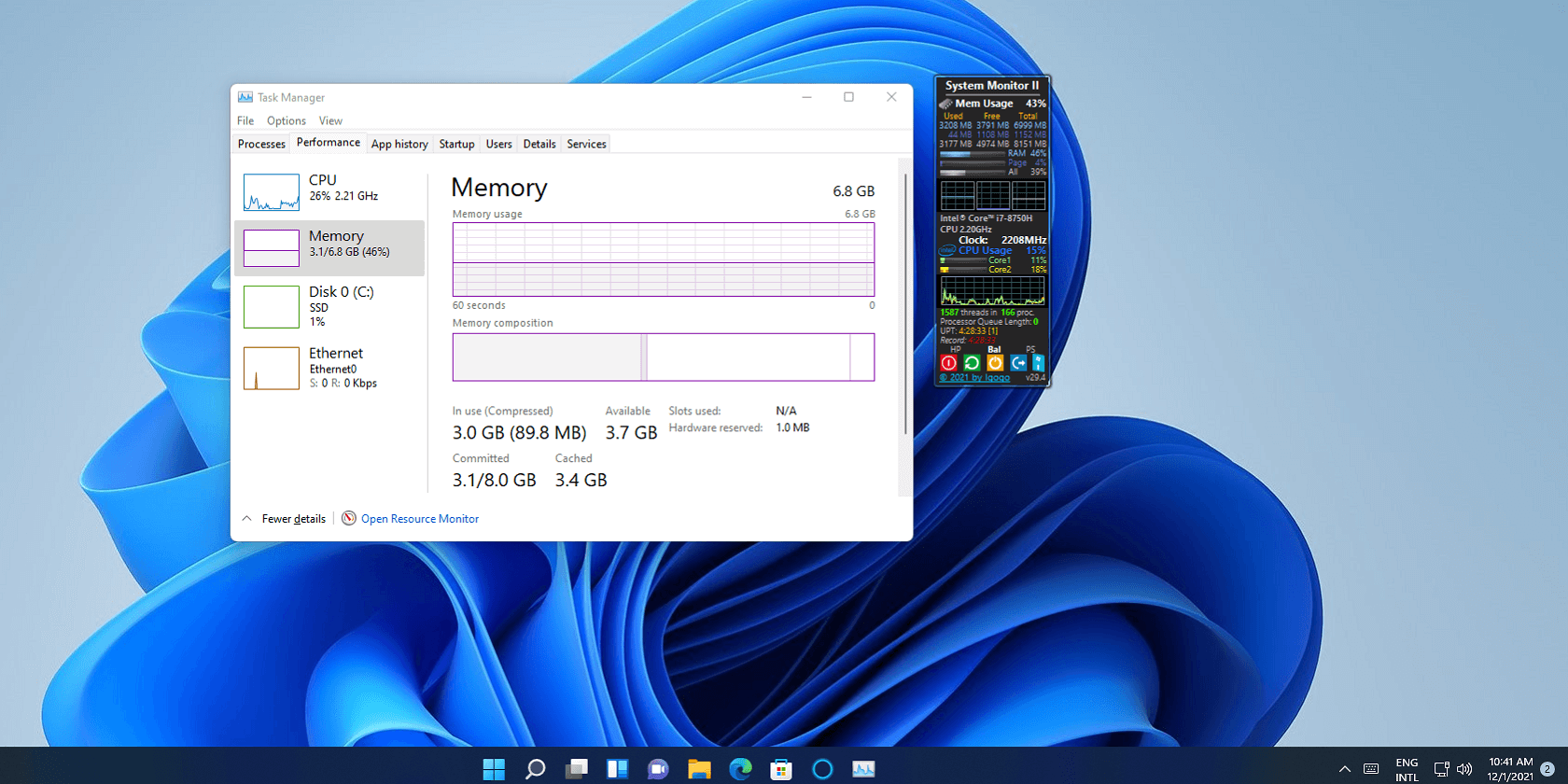
- To check if someone else is logged into your Windows system, visit the Task Manager by right-click on the taskbar.
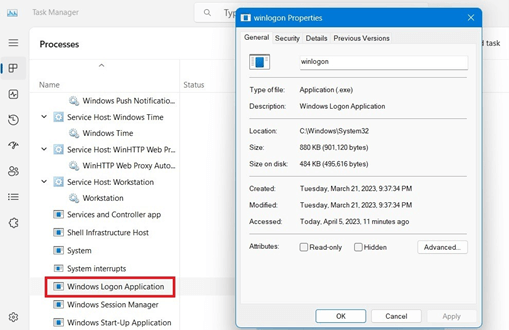
- Enter the background procedures and go to Windows Login Application.
- A identical access, like “Windows Logon (1)”, could mean another user is accessing your computer.
- Right-click and end the program to stop the login. Additionally, you can check the “Startup” to identify any unnecessary programs that may be running.
- Disable these programs to prevent potential keyloggers in the PC from gaining access while Windows is booting.
- The essential programs in the Startup are audio-based codecs, your browser, and the SecurityHealthSystray.exe program.
2. Utilize Command Prompt For Detecting Risky Internet Networks
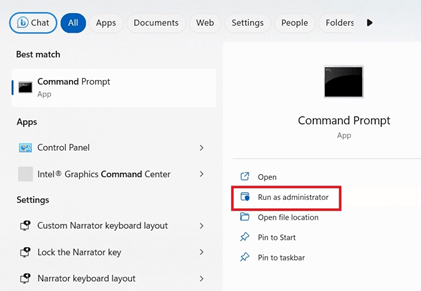
- Once you have made sure that nobody else has the login access into your computer, it is crucial to examine if there are any irregular network on your system.
- To detect keylogger in a Windows PC, open the Windows Command Prompt in Admin mode. All the programs and webpages connected to the internet on your Windows system will now be visible.
- Those connected to the Chrome, Microsoft Store, or Edge browser, “searchhost.exe,” “explorer.exe,” or other relevant applications like “svchost.exe” are secure.
- You can tell if malware tries to mimic a natural Windows process as there are tell-tale signs.
- The Prompt command lets you to choose and copy any content, with IPv6/IPv4 reports.
- You can validate these IP addresses on certain websites which defines the security and safety of the browser.
- No keylogger in Windows PC is present if the basis is your Google, ISP, or a Microsoft data center (for Chrome or Edge), or video conferencing or gaming apps.
3. Windows Security:
- Windows Security (formerly known as Defender) is a built-in tool for Windows that can discover the keyloggers in the PC when they enter the system.
- To access it, type Windows Security into the search option. On the location, you can check the security status of your device.
- Ensure all the safety characteristics have a green checkmark. In case of warnings, go deeper and fix the issue.
- Visit “Virus & threat protection” and check if any keyloggers are detected. If there are, the method prompts you to detain the risk.
- Visit “Manage settings” and setup “threat and Virus protection set up” for more alternatives. Allow every “Threat and Virus Protection Settings.”
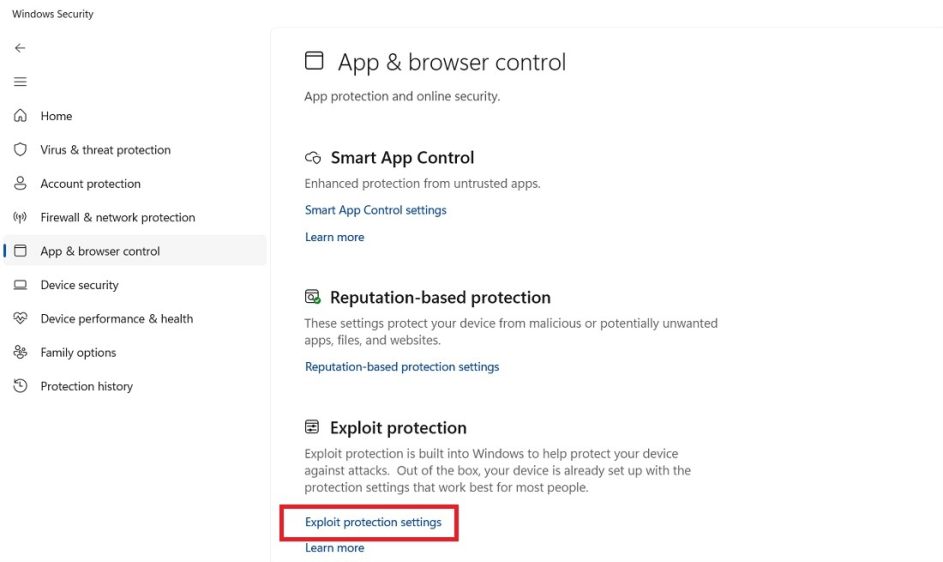
- Visit the “App & browser control” and choose “Exploit protection settings” to provide high-level protection from ransomware and rootkit attacks.
- Lastly, in “Device security,” make sure “Secure boot” and “Memory integrity” are both turned on to detect a keylogger in Windows PC and remove it.
4. Implement Anti- Malware Solutions:
- In addition to Windows Security, you can select outsourced anti- malware solution to protect yourself from kernel keylogger in Windows PC.
- Companies offer a free rootkit removal tool that is secure to use and does not trigger a warning from VirusTotal or Windows SmartScreen.
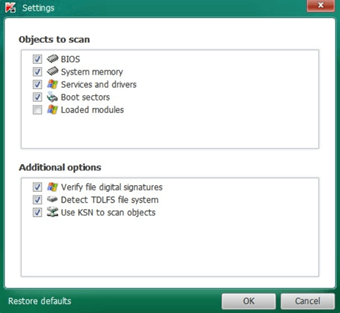
- Upon installation, you can initiate the scanning to appear for any potential kernel-method risks, with attached keyloggers.
- You can also adjust the settings to scan additional objects, although a system reboot is essential.
- The scan is quick and won’t strain the Windows device to detect keylogger in Windows PC.
- If no threats are found, the software intimates you, and if any Trojans or malware are present, the system detects and removes them routinely.
5. Identify Keyloggers Utilizing “Databases & Features:
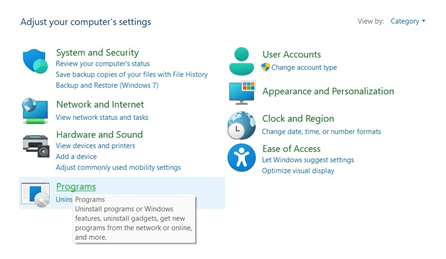
To remove suspicious or unknown applications, open the Control Panel in the search bar and connect to “Programs.” From there, you can right-click on any programs to uninstall them.
6. Reset The Windows PC:
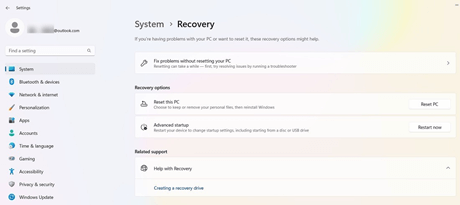
Cleaning up your Windows machine of malicious code like hypervisor-keyloggers can be efficiently done with a cloud-based reset. You won’t lose any of your data as the reset is done remotely and does not utilize local files. There are few ways to effectively identify hypervisor keyloggers in Windows PC since they can remain undetected and hidden in a virtual environment. Besides a cloud reset, there is little that can be done.
Keyloggers Protection In Windows PC:
A well-designed commercial grade keylogger in PC typically operates without any impact on system performance. It disguises any data sent to a remote operator as standard files or traffic. The preventative measures to help protect your computer from keyloggers. Here are some of them:
1. Constant Updating: The most effective way to ensure your computer is secure is to enable automatic cloud-delivered protection in the “Virus & threat protection” settings, allowing your system to receive security and intelligence updates even when idle. It will ensure you always have the latest version of Windows Security and all the security fixes necessary to stay safe.
- Windows 11, the updates are under “Settings -> Windows Update.”
- In Windows 10, the option is under “Settings -> Windows Settings -> Update and Security.”
2. Implementing Robust Keystroke Encoding: Keystroke encoding is an excellent way of thwarting keylogging. It scrambles all your keystrokes while they are sent to the internet. If an attack using a Keylogger in Windows PC at the hypervisor level has been successful, the malware can only discover random and encrypted characters. Multiple anti-keylogger solutions are dependable, malware-free, and utilize keyword encryption. Downloading, installing, and rebooting the system is very simple.
After the installation, you should enable it from the system tray on the right. You can switch on the option to protect you from keystroke profiling in the settings. Additionally, there are several encryption alternatives for your keystrokes. The feature directs the typo pattern to prevent websites from profiling you through the method of typing.
Conclusion
It is vital to stay alert regarding your digital safety since detecting keyloggers in Windows PC are one of the most widespread types of spyware and can be tough to identify and eliminate. If you think that your system is contaminated with a keylogger, take the appropriate action to delete it without delay. Keep your system current, use secure browsing habits, scan for malware frequently, and utilize reliable antivirus software to ensure that you remain protected against any spyware threats.
Frequently Asked Questions
1. What are the indicators that keylogging is taking place?
If you notice that your computer is running slower than normal, you see pop-ups and advertisements you didn’t request, or if you see a change in your browser or search engine settings, these could all be signs of a keylogger infection. To determine the cause of the issue, you can use the techniques previously mentioned.
2. Can keyloggers operate without being detected?
If you think you may have a keylogger or other malicious software on your computer, doing a free virus scan is a good idea. However, remember that the scan may not detect some advanced spyware or other forms of malware.
3. Are keyloggers present on all company laptops?
Certain organizations may have a policy in place to install keylogger software on their employees’ laptops. It could lead to administrators having access to confidential information stored on the device.
Popular Post
Recent Post
Advanced System Settings on Windows 11: Complete Guide
Windows 11 is a powerful operating system. It comes with many features that most users never explore. One of the most useful areas is the System Properties panel. This is where you can control how your computer performs, starts up, and handles memory. Many users only change basic settings like wallpaper or display options. But […]
21 Advanced Windows Security Settings: Latest Updates
Introduction: Your computer holds a lot of important data. From personal photos to work files, everything sits on your Windows system. That is why protecting it properly matters more than ever. Windows security settings have come a long way. Microsoft keeps adding stronger layers of protection with every update. Most users never go beyond the […]
Security Upgrades of Microsoft Windows in This Decade [Complete Guide]
Introduction Microsoft has been working hard to make Windows safer every year. Cyberattacks are growing fast. Hackers are smarter now. They target millions of Windows users every single day. That is why Microsoft has added many powerful new security upgrades of Microsoft Windows since 2020. These upgrades protect your data, your identity, and your device […]
How To Link a Microsoft Account to a Digital License on Windows [2026]
Most people never think about Windows activation until it suddenly stops working. Something as simple as replacing hardware or reinstalling Windows can cause the system to lose its activated status. Linking your Microsoft account to your digital license beforehand helps prevent unnecessary trouble and makes activation recovery much easier later on. Many people using Windows […]
Monthly Round Up: All Big Incidents Happened for Windows Users in The Month of April 2026
Windows users had a turbulent April 2026. On April 14, Microsoft rolled out its scheduled Patch Tuesday security updates, a routine release meant to close vulnerabilities and resolve known issues. What followed was anything but routine. Rather than strengthening systems, the updates triggered a cascade of fresh problems across Windows 10, Windows 11, and Windows […]
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]
Change Time Format On Windows: Complete Guide
Windows show time in different ways. Some people prefer the 12-hour clock with AM and PM. Others like the 24-hour format, also called military time. Knowing how to change time format on your Windows PC is a simple but useful skill. It helps you stay comfortable with your display and avoid confusion. Many users never […]
How To Get Help With Paint In Windows [2026]
Microsoft Paint has been around for decades. It comes with every version of Windows and is one of the easiest tools to use. But even simple tools can cause trouble. If you have ever felt stuck while drawing or editing an image, you are not alone. Many people look for help with Paint in Windows […]