Cybersecurity Tips for Remote Workers
Many businesses are adopting the remote work style for their operations, allowing employees and employers more flexibility. Indeed, a lot of remote workers utilize their personal devices, and they can access their work files from any location. However, that can pose some serious issues, like weak passwords as per ExpressVPN’s research, standard-level cybersecurity support, etc.
Indeed, accessing official accounts through personal devices can open more routes for hackers, malware, and other security issues to bypass the set defenses. Thus, there are some important steps you should take to minimize the potential problems, as per security experts.
Security Common Security Concerns for Remote Work?
A remote work lifestyle can be safe, but all participants need to pay better attention to cybersecurity concerns and take proactive measures. Using business-grade collaboration tools and security protocols should help with this protection, even with the less advanced system setup at home.
Here are some recommendations for employers to prepare their staff with better cybersecurity measures while working remotely.
- Inform employees about potential threats– Employers should provide a list of potential cybersecurity issues one might notice without the data encryption and firewall support that office-based systems can provide. Statistics showed that 9% of companies took measures to safeguard their remote employees from internet-centric attacks when they browse the internet.
- Prepare MFA support for data protection– Officials of a company can adopt the MFA technique to protect the company data better. The double layers of authentication steps can stop hackers from progressing more into company data.
- Prepare a continuity strategy for your business– In this case, employers must primarily center around remote security. Study the systems and how they work, what data types users are focusing on, etc. Based on these insights, one should plan the cybersecurity strategy fit for the workspace.
- Train employees about phishing attacks– Many companies get phishing attacks often, which is harder to deal with remotely for some employees. So, the business organizers should prepare informative training sessions for all staff members on how to identify different phishing attack types.
Best Tips for Protective Cybersecurity for Remote Workers
These are some of the most important steps remote workers themselves can take to safeguard their cybersecurity condition. Some measures are slightly technical, while others require simple steps. But, for the best cyber-use protection, use multiple of these measures.
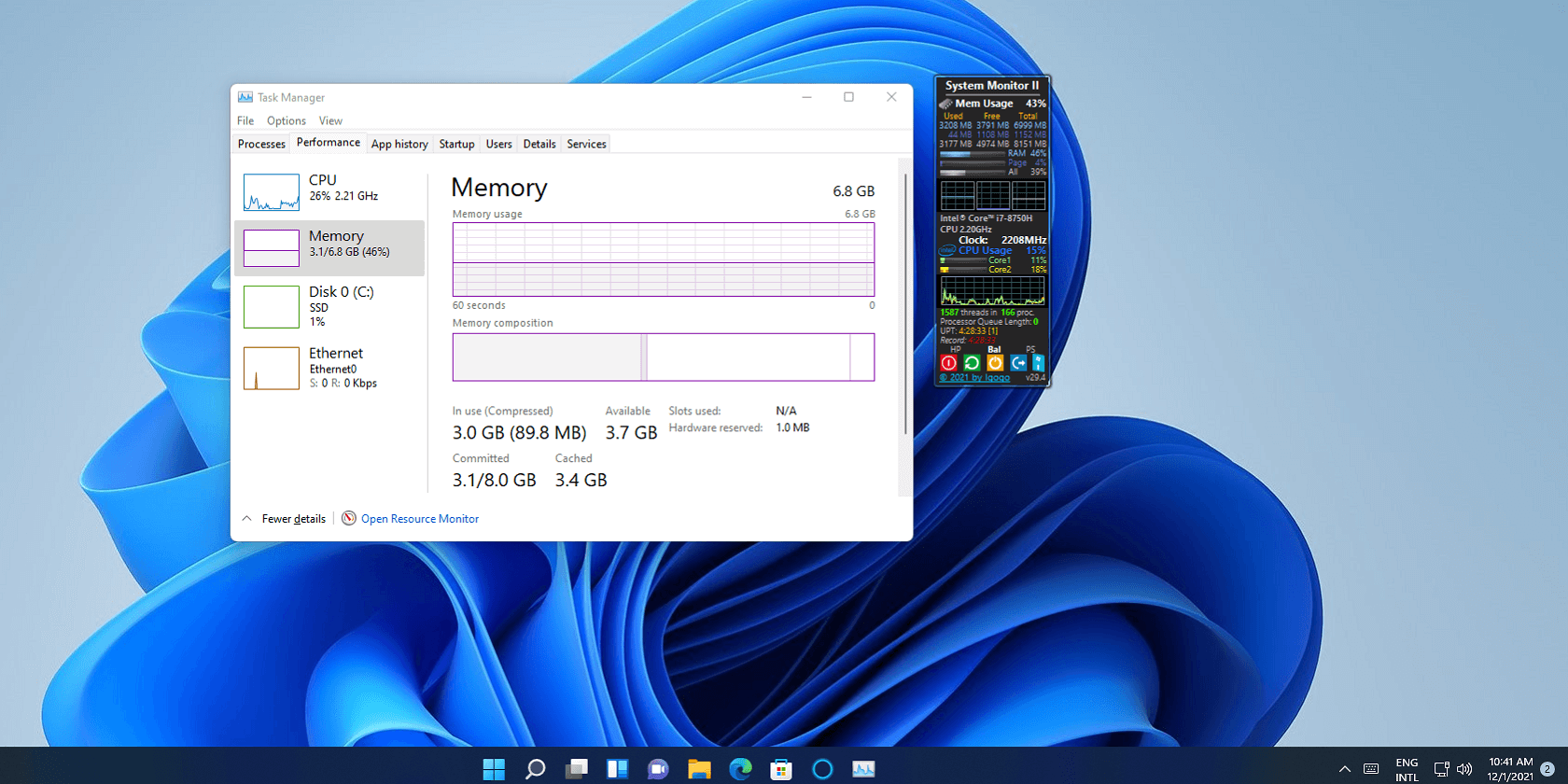
1. Avoid delaying software updates
The devices you use will provide software update notifications often, and it is important to follow through with this practice. Indeed, install the new software update for your app, like antivirus software that you have active, as soon as possible.
The latest upgrades of the software typically have fixed bugs and security flaws. In many cases, they are updated to catch newer malware or virus attacks that older versions could not detect. So, make sure to do regular device software updates.
2. Avoid deactivating the VPN
Many employees access the network of their workspace using VPN technology. This Virtual Private Network helps secure data transmission between two devices with strong data encryption support. Therefore, with the VPN active, it is possible to intercept cybercriminals from accessing company data, like customer information or documents.
The VPN software works automatically and assures strong background protection support, so do not disable it while handling remote work. Also, avoid public WiFi connections unless you have a reliable VPN switched on.
3. Make the home networks safer
It is possible to keep remote work-based cybersecurity conditions safe if you use a strong internet connection with proper security protocols in place. In the corporate sector, the IT Teams typically control the internet connection and assure automatic security for all employees. However, in the remote work model, people cannot get the same support from IT professionals in the home networks.
Thus, take specific measures to strengthen the home network security.
- Set a unique SSID name- You can reach your router’s Settings page and update the name of the SSID (Service Set Identifier) you are using.
- Learn more about the router– Access the settings page of the route you are using to learn more about the network you are using. The default IP address will be available here.
- Check and change the password– Many employees use basic-level passwords, even with work accounts. In fact, statistics show that 59% of adults in the US use their names or birthdays in passwords.
You can refer to ExpressVPN’s research to know more about such password options that people commonly utilize. However, you should set a more unique and longer password with various diverse characters for a better safety guarantee.
- Run the latest firmware for your router- New software patches are available for router devices in the firmware, so check if new updates are available. Then, run the upgrade in your system.
4. Opt for secure business tools
Some collaborative productivity and business tools are available that are preset with high-quality encryption and security protection. Many of them run with cloud protection that helps with privacy protection, secure data transactions, and more storage.
Many companies in different industries need compliance guaranteed with protocols for accidental deletion, unauthorized access, and cybersecurity protection for their employees. These relate to all work-related activities like file sharing, video conferencing, and chatroom usage. For better cybersecurity protection with your remote work, you can use these home tools to connect and work on your tasks.
5. Multi-factor authentication is useful
Indeed, it would be best to consider adopting multi-factor authentication as a security measure during remote work processes. This adds a secondary layer of protection to online account access, like the work data, files, computer network, device, etc.
With this measure, users can set multiple rounds of identity protection to account access, like two or more authentication moves when trying to log in. Common measures in this context are security tokens, passwords, and biometric identification (fingerprint or face sensor).
Conclusion
Indeed, there are different types of cybersecurity approaches you can take to safeguard against varying steps while working remotely. Of course, some measures will work best for your work condition.
Before choosing, try out many of these tips and operate as many as possible. So, study your options well here. Properly keeping track of your cybersecurity condition directly should help with better protection during remote work.
Popular Post
Recent Post
Fortect Driver Updater Review: Features, Steps, Pros, and Cons.
A new PC usually feels quick and responsive. Applications open instantly, games run smoothly, and everything works as expected. As time passes, however, you may notice slower performance, system crashes, hardware glitches, or devices that stop working properly. While many people assume malware or low storage space is to blame, outdated drivers are often the […]
New Features Coming in Windows 11 This Year [2026]
Microsoft is always working to make Windows better. This year is no exception. The company has announced and rolled out several exciting updates for its users. These updates touch almost every part of the operating system. From the Start menu to system settings, changes are arriving fast. If you use Windows daily, you will want […]
Top 14 Duplicate Photo Finder and Remover For Windows [2026]
Introduction: Photos pile up fast. Well, yes! You take ten shots of the same moment. You download the same image twice. You back up your folder and forget you already did it. Before you know it, your storage is packed with copies. A good duplicate photo finder helps you take back that space without losing […]
Advanced System Settings on Windows 11: Complete Guide
Windows 11 is a powerful operating system. It comes with many features that most users never explore. One of the most useful areas is the System Properties panel. This is where you can control how your computer performs, starts up, and handles memory. Many users only change basic settings like wallpaper or display options. But […]
21 Advanced Windows Security Settings: Latest Updates
Introduction: Your computer holds a lot of important data. From personal photos to work files, everything sits on your Windows system. That is why protecting it properly matters more than ever. Windows security settings have come a long way. Microsoft keeps adding stronger layers of protection with every update. Most users never go beyond the […]
Security Upgrades of Microsoft Windows in This Decade [Complete Guide]
Introduction Microsoft has been working hard to make Windows safer every year. Cyberattacks are growing fast. Hackers are smarter now. They target millions of Windows users every single day. That is why Microsoft has added many powerful new security upgrades of Microsoft Windows since 2020. These upgrades protect your data, your identity, and your device […]
How To Link a Microsoft Account to a Digital License on Windows [2026]
Most people never think about Windows activation until it suddenly stops working. Something as simple as replacing hardware or reinstalling Windows can cause the system to lose its activated status. Linking your Microsoft account to your digital license beforehand helps prevent unnecessary trouble and makes activation recovery much easier later on. Many people using Windows […]
Monthly Round Up: All Big Incidents Happened for Windows Users in The Month of April 2026
Windows users had a turbulent April 2026. On April 14, Microsoft rolled out its scheduled Patch Tuesday security updates, a routine release meant to close vulnerabilities and resolve known issues. What followed was anything but routine. Rather than strengthening systems, the updates triggered a cascade of fresh problems across Windows 10, Windows 11, and Windows […]
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]