What is brand risk protection and why does it matter?
Today’s security professionals have become familiar with the idea that every organization has an attack surface that describes its global exposure to threats against internal and cloud applications, devices, users, and data.
The attack surface grows as greater connectivity, cloud applications and myriad new types of device are adopted as an organization expands its digital footprint. It follows that when a security team calculates an organization’s attack surface, what they are really doing is estimating its vulnerability to cyberattack.
However, the idea of the attack surface isn’t always terribly helpful because it assumes that an organization has the tools to understand its true size. As countless successful cyberattacks demonstrate, organisations often discover after the fact that their attack surface was larger than they’d realized.
Brand Risk Protection (BRP)
One issue is that parts of the attack surface are easy to miss because they exist in the public sphere beyond the traditional responsibility of the IT department. It is these sorts of vulnerabilities Brand risk protection (BRP) services are designed to detect and address.
Broadly speaking, BRP defends an organization’s brand and the way this can be manipulated, exploited, and hijacked to deceive customers. It’s a huge and expanding area that includes discovering assets, monitoring for threats, remediating attacks, and managing the organizational processes involved in doing this. The main areas include:
Domain protection – a way of monitoring an organization’s web domains, now routinely targeted by typo-squatters (lookalike web names called homoglyphs) and domain/subdomain impersonation. This has been a problem for many years and is the bedrock of phishing attacks as well as copycat domains selling fake merchandise.
Brand and social media protection – monitoring the web and social media channels for brand impersonation using lookalike or hijacked accounts which abuse trademarks, logos, employees, and brand imagery.
Phishing detection – monitoring threat intelligence, domain registrations and MX record changes for information on phishing campaigns targeting an organization’s employees or customers.
Data leaks – data and credentials stolen from customers, or lists of fake and hijacked accounts, now flood the dark web, deep web, and Telegram channels, where they are traded back and forth. In many cases, organisations are not aware this data has even been taken, which makes DRP detection useful intelligence.
Account, VIP, and social media protection – monitors for stolen and fake employee accounts on channels such as Facebook, Twitter, LinkedIn, and Instagram.
Fake mobile apps – once rare, the use of lookalike mobile apps has grown with their importance to customers. Often served from third-party app stores, these can be difficult to spot.
Disinformation, misinformation, and fake news – an area of growing concern is false information planted to damage a brand’s reputation. A 2019 study by the University of Baltimore estimated that disinformation now costs the global economy $78 billion each year, with even one negative article on a search pages causing a 22% loss of business. Campaigns can also be used to alter a company’s stock price. Disinformation used to be politically or nationally focused but is increasingly being used against businesses for reasons of economic advantage.
What unites all BRP categories is that they are almost impossible to detect using conventional security tools. When they are detected, it is often by employees in departments beyond IT, for example a marketing department that receives complaints about brand impersonation. If an abuse is not detected or is detected by someone without the means to do anything about it, this type of abuse can slowly proliferate.
How does BRP work?
BRP is usually offered as a suite of integrated tools which detect risks using a mixture of automated machine intelligence, threat feeds, and manual processes. The nature of monitoring depends on the threat being assessed. Domain abuse is carried out by analyzing registered domains for ones that look similar to protected domains. Protecting brands is basically the same process conducted on social media or the web, or by constantly searching for specific brand images, product names, email addresses, or leaked credentials.
BRP remediation
What distinguishes one BRP system from another is the effectiveness of the remediation features on offer. This can be a complex undertaking because once detected each must be tackled individually and that involves managing a detailed task workflow over extended periods of time.
Ideally, the BRP service should offer a single view of the risks being tracked, with the tools to take down or report counterfeit sites and content, liaising with law enforcement where appropriate. It’s also important that the service can accommodate non-technical employees in departments such as marketing who are increasingly being given the job of tracking brand abuse and disinformation.
Conclusion: don’t ignore brand risks
Perhaps the biggest innovation of BRP is really that it brings together a suite of capabilities that have existed in an ad-hoc way for years, but which weren’t integrated couldn’t scale as abuse increased. Managing digital risks in this informal way is expensive and is bound to miss problems. Integrating BRP mitigation in a single platform is the simplest way to make abuse visible to an entire organization.
Popular Post
Recent Post
How To Link a Microsoft Account to a Digital License on Windows [2026]
Most people never think about Windows activation until it suddenly stops working. Something as simple as replacing hardware or reinstalling Windows can cause the system to lose its activated status. Linking your Microsoft account to your digital license beforehand helps prevent unnecessary trouble and makes activation recovery much easier later on. Many people using Windows […]
Monthly Round Up: All Big Incidents Happened for Windows Users in The Month of April 2026
Windows users had a turbulent April 2026. On April 14, Microsoft rolled out its scheduled Patch Tuesday security updates, a routine release meant to close vulnerabilities and resolve known issues. What followed was anything but routine. Rather than strengthening systems, the updates triggered a cascade of fresh problems across Windows 10, Windows 11, and Windows […]
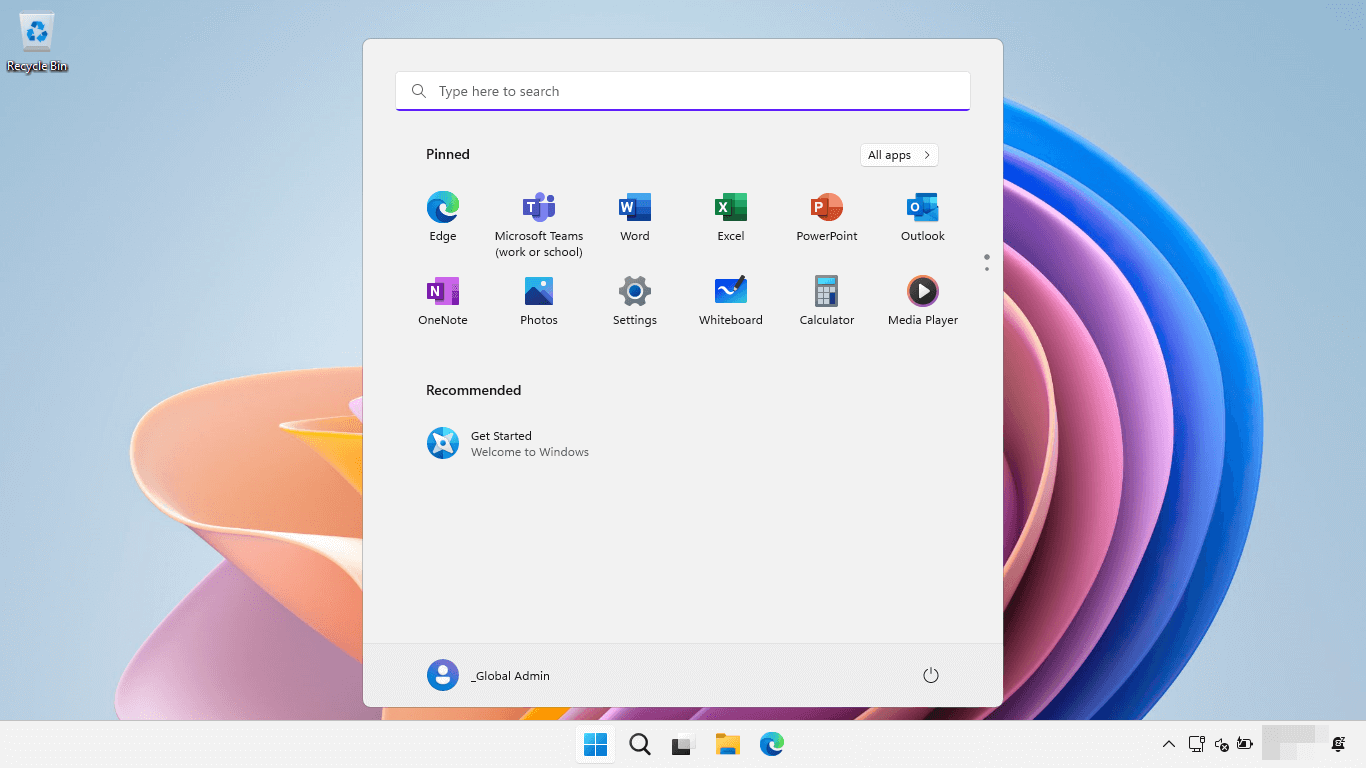
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]
Change Time Format On Windows: Complete Guide
Windows show time in different ways. Some people prefer the 12-hour clock with AM and PM. Others like the 24-hour format, also called military time. Knowing how to change time format on your Windows PC is a simple but useful skill. It helps you stay comfortable with your display and avoid confusion. Many users never […]
How To Get Help With Paint In Windows [2026]
Microsoft Paint has been around for decades. It comes with every version of Windows and is one of the easiest tools to use. But even simple tools can cause trouble. If you have ever felt stuck while drawing or editing an image, you are not alone. Many people look for help with Paint in Windows […]
How To Toggle Bluetooth Settings Easily on Windows [2026]
Bluetooth is a key feature on any Windows computer. It allows you to connect devices like headphones, keyboards, mice, and speakers without using wires. Many users rely on it daily, so it helps to know how to switch Bluetooth on or off quickly whenever needed. Sometimes you just want to turn Bluetooth on or off […]
System Restore: Complete Guide for Windows 11
Introduction: Your Windows 11 PC can run into problems at any time. A bad update, a new app, or a wrong setting can break things fast. When that happens, you need a quick fix. System Restore is one of the best built-in tools Windows offers for these moments. It helps you roll back your PC […]
Setting Up Default Audio Device: Complete Guide [2026]
Introduction: Sound is a big part of how we use computers every day. Whether you are watching a movie, joining a video call, or listening to music, your audio needs to work properly. Setting up default audio device is one of the first things you should do when you connect new speakers, headphones, or a […]