How to Stop Companies From Collecting Your Personal Information?
Introduction
With the increased focus on development and technology, most people use various digital devices for their daily tasks. Elements like IoT, wearables, and smartphones are common accompaniments for most people today for personal and professional use. However, such software always collects customer data, like browsing history, health data, GPS location tracking, etc.
Many companies collect user details for their products, like personal identity, address, IP address, and more. Therefore, it is vital to use the right preventive measures to stop companies from acquiring personal customer data, like with identity protection software.
Read ahead to know the different methods you can take to protect consumer data from digital devices, third-party service providers, and businesses.
Methods to block companies from getting customer data
Businesses in different industry verticals, organizations, and service providers collect customer details like identification, location status, payment information, etc., for streamlined performance. However, this can open you to external cyber-attacks, data thefts, and potential malware damage.
We looked through the known solutions to protect consumer data and compiled this list of the best ways to combat unauthorized digital data collection.
Solution 1: Download and Utilize a VPN
Using a VPN or Virtual Private Network is one of the most effective ways to protect one’s personal data while using online services. People often browse the internet while they are using public WiFi or a network. Even in privatized intranet within companies, there is the potential of connecting to one server system between multiple users.
You can use suitable VPN software like NordVPN to keep public browsing safe and defend all users’ online activity and movement data. This VPN service provider has more than 5500 servers across 60 countries, making it simple to access and use for most global users. You can privately search for content, access services like streaming videos from other countries, and safeguard yourself from dark web monitoring.
Solution 2: Opt for ad-blocking and anti-tracking tools across all devices
While searching for content or filling up any form, sites produce tracking cookies that reach users’ devise. These small-scale files in the browsers trace users’ online activity across websites and identity them.
A suitable solution is to apply anti-tracking extensions for mobile devices and desktops, like Adblock Plus. It blocks the tracking cookies from collecting any data without the user’s permission. The extensions work as browser add-ons and are compatible with most devices/platforms. Moreover, they stop ads and block third-party trackers efficiently.
Solution 3: Avoid using a tracking-centric search engine
For most people, Google is the main search engine of choice for their online activities and browsing. However, high-scale organizations like Google create user profiles and acquire data for analytical insights from past web activity and search history. Common reasons include understanding customer persona and requirements to promote targeted ads.
On the other hand, some search engines like Startpage do not ask for private user information or store it for external usage.
Solution 4: Study the privacy agreements carefully and configure settings
Some websites and applications do collect a certain amount of user information for operations. For example, for apps that allow users to order food online, data tracking and GPS location tracker activation are necessary for the software to find your correct location.
A common mistake many users make while downloading a new app or signing up for a service or account is not reading the fine script, i.e., privacy policies and T&C details. Not reading it and giving permission to the company can allow them to collect, use, and distribute your personal data as they need. Read the privacy and terms of service details to understand if you permit more complex matters than is acceptable.
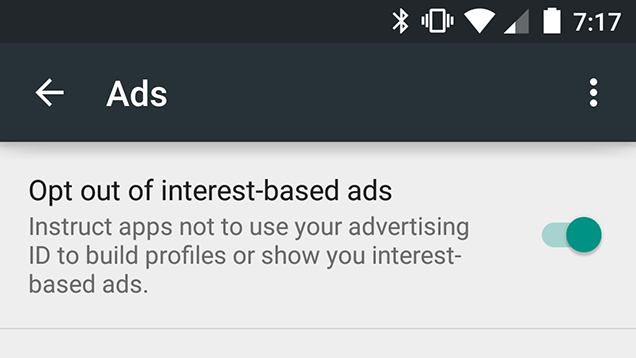
You should access the settings and make adjustments to the preferences as necessary. For example, there is an Ad preference-related page on Google. In addition, you can go to the settings and switch off personalized ads from your account.
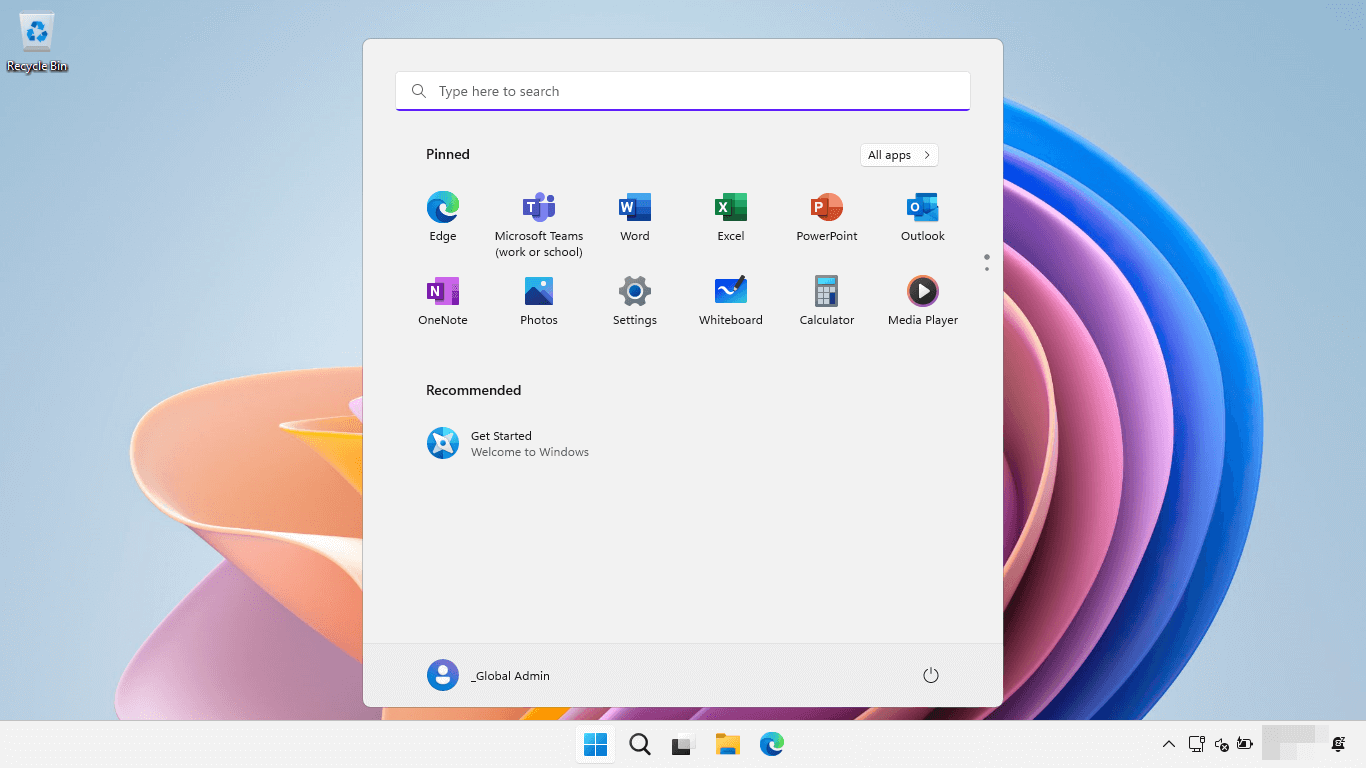
How to Do This (via Android smartphone)?
Step 1: Open your smartphone device and access the main menu.
Step 2: Go to the Settings section.
Step 3: After the Settings menu opens, scroll down to the “Accounts” option and click on Google.
Step 4: On the next page, open Privacy > Ads.
Step 5: Click the check box off for the “Opt-out of interest-based ads” prompt under the Ads sub-menu.
Step 6: Close the Settings and return to regular browsing.
Solution 5: Avoid phishing scams
Many of the emails people receive are automated alerts or notifications from different companies. However, some email types from unknown senders can get jumbled among the various emails.
It is best to avoid opening these emails or clicking on the given links since they may be phishing or ID theft hacking attempts. Block any contact that continuously sends spam messages and inform the service provider about these messages. You can also use antivirus software to keep our phishing attacks due to its Anti-Scam Protection feature.
Solution 6: Activate Multi-Factor Authentication
While entering or registering an online account through another device, the service provider asks for permission to allow automated sign-in details. In addition, some sites ask multiple times for users to access a site or service, even when they reload the site after a few seconds of inactivity.
Service providers that allow 2FA or MFA password protection to enter accounts are more reliable options. Here, the software activates multiple steps of ID authentication, like Pincode, OTP, and fingerprint ID. Enable these features for extra security and control the limit of personal data companies can acquire or store.
Solution 7: Use a Password Manager
One of the most common manners of losing control over one’s personal information and how much companies can collect is forgetting one’s password. Many users set weak or generic passwords or use the same option for different accounts. Unfortunately, this is not strong enough to block hackers, who can acquire access quickly.
You should download and use a high-quality password manager like NordPass or Norton 360 Password Manager. With this software, you can securely store all account passwords in one location and even create new and unique random passwords for different accounts.
How to Use This?
Step 1: After opening the Norton Password Manager on the browser, choose its icon from the top-right side. Sign in to the account.
Or directly download the software extension and launch it.
Step 2: Set up the online vault and import your account information, passwords, and other information from different sites in it. Create a master password, as directed under the software.
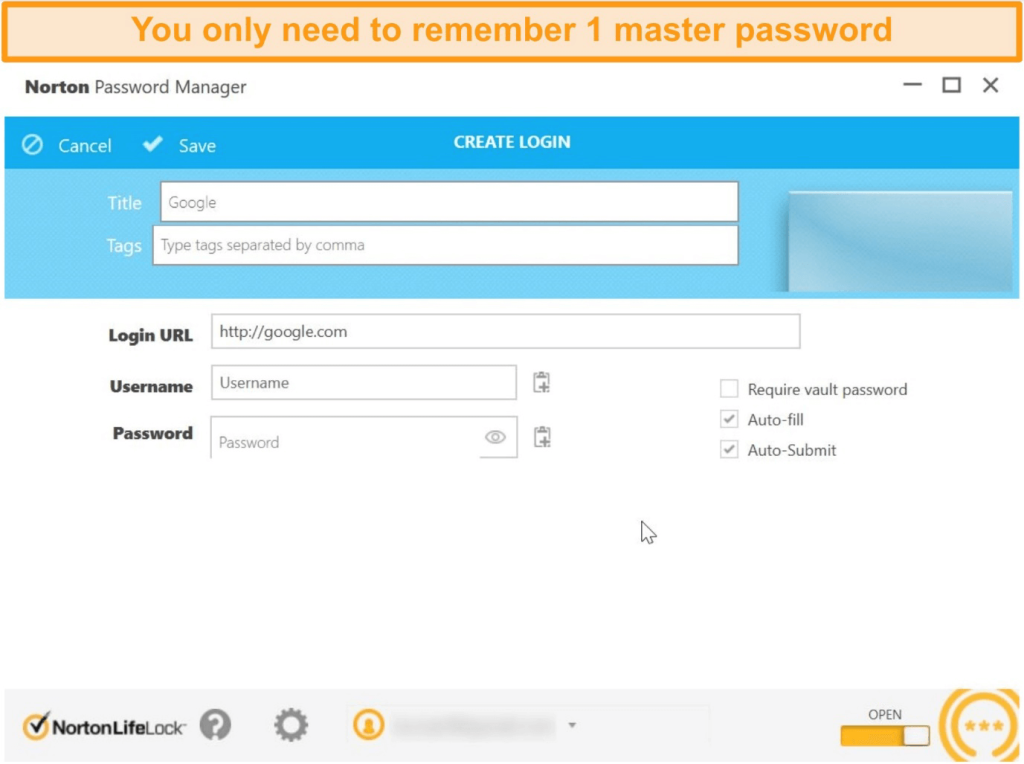
Step 3: the app would send occasional alerts about updating, saving, or filling up data in the vault.
Solution 8: Use an Identity Protection Software
To protect consumer data, you can opt for an all-in-one identity protection software like Systweak Advanced Identity Protector. This tool lets users keep their private data, like credit card information, email accounts, passwords, credential data, social security numbers, etc., completely private.
The app is simple to install and use on both Windows and Mac devices. The software stores all sensitive information in the pre-set Secure Vault for added protection or delete them if necessary. The software scans for faulty or unprotected details and carefully organizes all details in the vault for encrypted protection.
Through the Secure Vault, you can find details like account and password information quality across the connected devices.
Conclusion
You can use multiple techniques to safeguard your personal data from companies across different platforms. For example, you can download and apply a VPN service or use ad-blocking extensions/tools on your device. Alternatively, you can operate a specialized identity protection software like Systweak’s app or safeguard all details within a Password manager.
Try out multiple of these techniques to protection your details online before finalizing one method that suits your needs best.
Popular Post
Recent Post
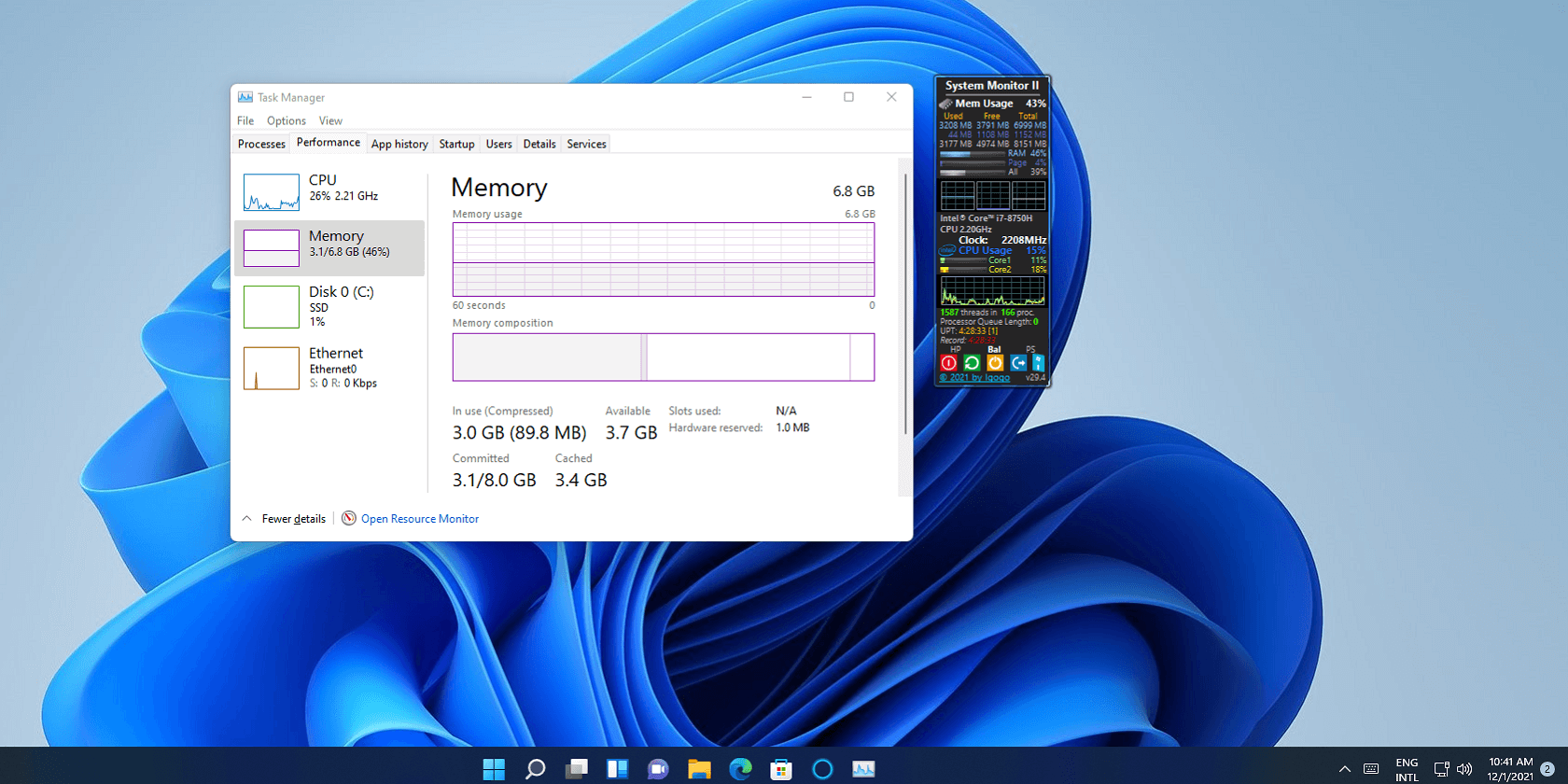
How To Add Or Remove Programs On Windows 11: 4 Quick Methods to Try.
Introduction: Managing software on your computer is something every Windows user should know. Whether you want to install a useful new app or remove programs you no longer need, understanding how to add remove programs can help your PC stay clean, organized, and fast. It also helps free up storage space, reduce clutter, and improve […]
Monthly Round-up: All big cybersecurity incidents happened in the Month of April 2026
April 2026 was one of the most eventful months in recent cybersecurity history. Well, yes. Attackers did not just target one industry or one country. They went after hospitals, government bodies, travel platforms, water utilities, education companies, and healthcare technology firms. The scale and variety of these attacks made it clear that no organization is […]
How To Change Your Default Web Browser Windows 11 And 10 [Complete Guide]
Your web browser is the gateway to everything you do online. It opens your emails, plays your videos, and loads your favorite websites. But what if the browser that opens every time is not the one you like? That is a small problem with a very easy fix. You can change your default web browser […]
Change Time Format On Windows: Complete Guide
Windows show time in different ways. Some people prefer the 12-hour clock with AM and PM. Others like the 24-hour format, also called military time. Knowing how to change time format on your Windows PC is a simple but useful skill. It helps you stay comfortable with your display and avoid confusion. Many users never […]
How To Get Help With Paint In Windows [2026]
Microsoft Paint has been around for decades. It comes with every version of Windows and is one of the easiest tools to use. But even simple tools can cause trouble. If you have ever felt stuck while drawing or editing an image, you are not alone. Many people look for help with Paint in Windows […]
How To Toggle Bluetooth Settings Easily on Windows [2026]
Bluetooth is a key feature on any Windows computer. It allows you to connect devices like headphones, keyboards, mice, and speakers without using wires. Many users rely on it daily, so it helps to know how to switch Bluetooth on or off quickly whenever needed. Sometimes you just want to turn Bluetooth on or off […]
System Restore: Complete Guide for Windows 11
Introduction: Your Windows 11 PC can run into problems at any time. A bad update, a new app, or a wrong setting can break things fast. When that happens, you need a quick fix. System Restore is one of the best built-in tools Windows offers for these moments. It helps you roll back your PC […]
Setting Up Default Audio Device: Complete Guide [2026]
Introduction: Sound is a big part of how we use computers every day. Whether you are watching a movie, joining a video call, or listening to music, your audio needs to work properly. Setting up default audio device is one of the first things you should do when you connect new speakers, headphones, or a […]
Emptying the Recycle Bin In Windows: Complete Guide
Introduction: When a file is deleted in Windows, it is not erased immediately. It is first sent to the Recycle Bin, where it stays until it is removed permanently. Clearing the Recycle Bin is a quick way to regain storage space. Many users do this often to keep their system clean and working properly. Knowing […]
How To Close Games Assist: Simple Methods to Try
Introduction Do you have a feature on your device that keeps popping up while you play games? Many users want to know how to close Games Assist because it shows up at the wrong time. It can be distracting. It can slow down your game. And sometimes, you just do not need it running in […]